This article is more than 1 year old
Dating app spent months as STALKING app
Tinder plugs leak that let you track your intended for months at a time, to within 30m
The popular dating app Tinder spent months last year leaking excessive location data about its users.
According to Include Security, the bug arose when Tinder implemented a fix to an older security issue that emerged in July 2013 (in which users could get other users' geolocation in latitude and longitude, discovered by the same company).
Tinder is supposed to let a user know if another user is in the same area as them – but Include Security notes that after its API was changed last year, it provided “me-to-you” distance (the distance_mi field) as a 64-bit double-precision number.
If Alice's distance is provided with that much precision, and Bob can get the distance from three locations, all he needs do is draw three circles, find the intersection (trilateration) and he knows Alice's location within 100 feet (about 30 metres).
Getting distance reported from three locations is easy, Include Security's Max Veytsman writes: with three fake accounts in the “target's” city, all that's required is to feed Tinder a different location for each fake account, and it returned the distance_mi value for each.
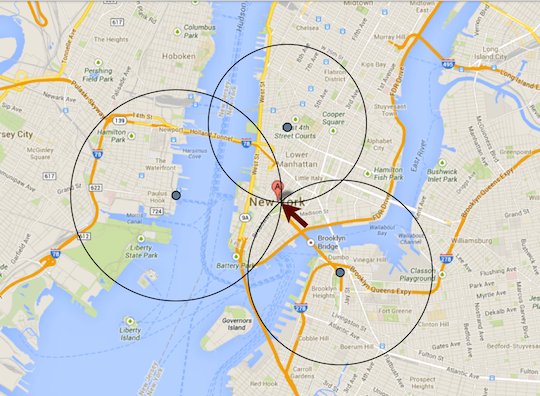
You are here: Include Security's Tinder data-leak demo
The issue, which was fixed by January 2, is demonstrated in this YouTube video:
As Veytsman notes, geodata leakage is a big issue in the mobile app space, because app writers are often insensitive about how they handle location information. Include Security's recommendation for Tinder is good advice for any mobile app handling location data: “never deal with high resolution measurements of distance or location in any sense on the client-side. These calculations should be done on the server-side to avoid the possibility of the client applications intercepting the positional information.” ®
