This article is more than 1 year old
iFrame attack injects code via PNGs
Old malware, new trick
Security vendor Sucuri is warning that it's spotted an attack in the wild that embeds malicious code in PNG files.
The iFrame injection attack loaded a valid jquery.js file with very little to alert even the researcher that something else was going on. As the company writes in this blog post, the only red flag in the code was a loadFile() function downloading dron.png into the iFrame.
As Sucuri's Peter Gramantik writes, the loading of the PNG is followed by a decoding loop, and this is where life gets more interesting. The decoding loop, he writes, is “taking the normal behaviour of an iFrame injection, embedding it within the meta of the PNG file, and just like that we have a new distribution mechanism.”
So the user doesn't notice anything happening, the iFrame is loaded at -1000px – meaning it's placed off-screen.
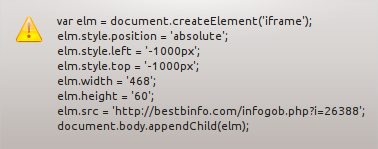
The payload turned up by Sucuri
Sucuri notes that the techniques used in this case could also be applied to other image types. Naturally, as the discoverer, Sucuris has added the attack to its scanner; El Reg expects other vendors will follow suit. ®
