This article is more than 1 year old
Dead Kim Jong-il's OS makeover takes a page from Dead Steve Jobs
New glorious people's UI brings fruity flavor to NORKS PCs
The latest version of North Korea's official operating system has been given a makeover that lends it an all-too-familiar look and feel.
The Norks have maintained a state-sponsored Linux distro – RedStar Linux – since 2010. The earliest version looked like a fairly stock KDE desktop Linux, for its time. But with the new version 3.0, Pyongyang's OS has taken on a decidedly Cupertinian flair.
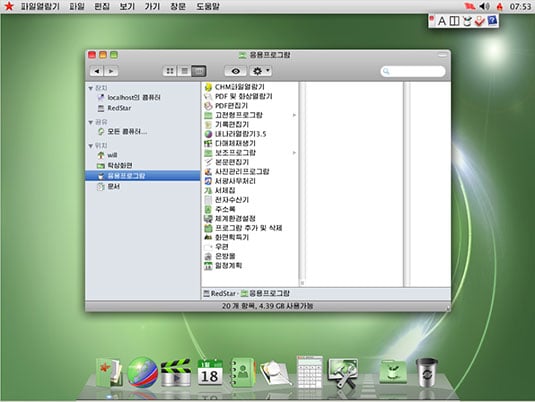
As shown in screenshots gathered by web hacker Will Scott – who spent last autumn teaching computer science in Pyongyang – a few vestiges of the earlier RedStar UI remain, but most of it has been scrubbed and polished to look remarkably like OS X.
A view of the desktop shows system menus across the top of the screen, Mac-style, along with an application launcher at the bottom of the screen that resembles the OS X Dock.
Windows in RedStar 3.0 borrow the Finder's brushed-metal look, and its icons and controls borrow liberally from Apple too, albeit with some variations. The buttons to close, minimize, and zoom the windows are rounded squares instead of circles, for example, and in place of the Apple logo it has (naturally) a red star.
RedStar's boot screen is a bit gaudier than that of OS X, in that it shows you an illustration of a computer. But curiously enough, the machine pictured resembles nothing so much as an early Intel-processor iMac, back when iMacs still came with optical drives.
Not that we're accusing North Korea of ripping anything off, mind you. According to his official biography [PDF], the Democratic Republic's former Leader Kim Jong-il spearheaded a technological revolution that enriched every North Korean with a "good knowledge of science and technology." And his youthful successor, Kim Jong-un, is of the Millennial Generation, born during the early PC era.

Where are you? If not in North Korea, remain where you are and wait for instructions (click to enlarge)
No, we rather suspect that the Norks have merely taken advantage of any of several existing ways of transforming a Linux desktop into an OS X lookalike – Mac4Lin and Macbuntu being but two.
As far as we know, however, Pyongyang doesn't bother to distribute the source code to RedStar, which presents some license-violation issues – but we'll leave the international trade disputes to President Obama and his diplomats. ®