This article is more than 1 year old
BT-owned ISP Plusnet fails to plug security hole on its customer signup page
Spaffs new user credentials all over the interwebulator
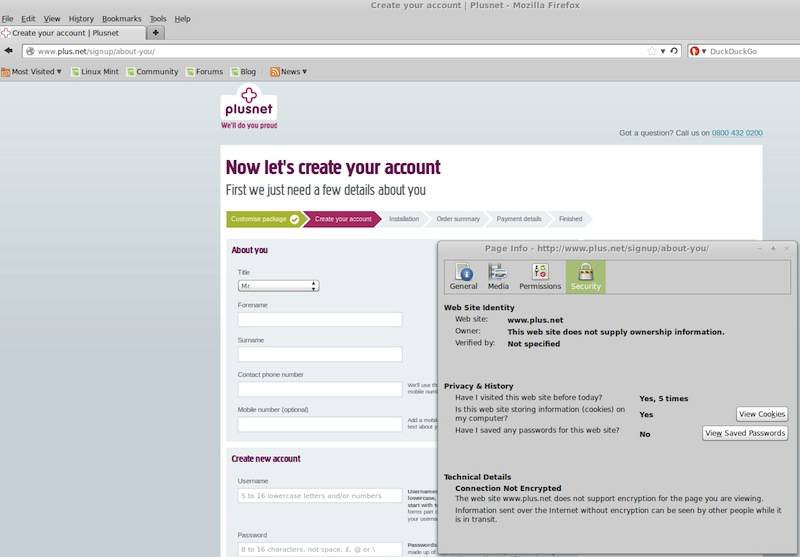
Exclusive Sheffield-based telco Plusnet isn't doing any of its new customers "proud" right now, after an anonymous source told The Register that the company was currently transmitting personal details over an unencrypted web page.
The firm, which is owned by telecom giant BT, is asking interested subscribers to fill in a form online that - when submitted - "can be seen by other people while it is in transit".
Incredibly, Plusnet was told about the obvious security blunder by our concerned source over two weeks ago.
We were told:
I was just shocked by the way the sales rep brushed off my reporting of this during the contract setup (after discovering the vulnerability I used the phone instead).
She assured me that the security team would deal with it right away. In my opinion, over two weeks is more than enough time to sort this out.
Also, factor in the point that (as many new customers ordering an initial broadband setup are likely to do) I was using an open Wi-Fi hotspot to visit their site!
Our source added that he had used a private VPN connection to sign up to the ISP, but noted that many ordinary folk will fill in the form, safe in the knowledge that an outfit owned by BT would surely have its security credentials in order.
Click here for a larger version of this screen grab
Another source told us:
Plusnet ... store user passwords in unencrypted form, as I learnt when considering opening an account with them last summer [yes, six months ago]. When I told the 'tech' person I was talking to that many of the credentials could be used to access users' accounts with third party services, he replied that that was impossible. Though he didn't say why. I got broadband from someone else in the end.
Vulture Central was easily able to replicate the Plusnet cockup via the Firefox browser.
Among other things, the form requires an individual's full name, telephone number, username and password. ®
Update
The Reg questioned the firm over its lax security measures for new customers and this statement was provided to us by a spokesman a few hours after we published the story:
All Plusnet customer passwords are stored with full encryption. Our customer sign up page is currently unencrypted, and we are in the process of fixing this urgently.
It would appear that the company only began working on a fix after we'd been in touch. Funny that ...
