This article is more than 1 year old
Glassholes, snapt**ts, #blabbergasms, selfies and PRISM: The Reg's review of 2013
12 months in 26 characters
It's all 'bout the money
K is for Ker-ching: Bitcoin is a virtual payment system that lived on the fringes of the web until this year, when interest exploded. The virtual currency’s value peaked on one Bitcoin exchange with a single Bitcoin worth $1,209.94 in November – its value having increased 100-fold during the year. More than 250 web retailers were accepting Bitcoin on Black Friday in the US, Richard Branson’s Virgin Galactic said it had accepted the virtual currency to pay for flights and US economics chiefs called Bitcoin a "legitimate service". The media became fascinated. The driver for all this was Dark Web (see N is for Nefarious), when it transpired the currency was being used to trade illegal goods and services. Crims liked the fact Bitcoin is not traceable: it's virtual and not owned or operated by a central source.

Don't blink, its value will half
To this end, the tabloid rise and take down of criminality exchange Silk Road was a big help in boosting its profile but this also made it look meme-ish, like this year's Second Life. Stability remained one of Bitcoin’s primary problems - by mid-December, the Bitcoin's value had slumped to half its November high. The number of Bitcoin transactions are not even a blip compared to the volume of real currency transactions by the likes of Visa and Mastercard. And if that's not omen enough, consider that Facebook antagonists the Winklevoss twins are betting heavily on Bitcoin. Now you know it’s doomed.
L is for #Loser: You thought you’d seen the worst in 2012 when social marketing “experts” embarrassed themselves and singer Susan Boyle by coming up with #susanalbumparty to promote the singer’s latest work.
2013, however, saw the #bubble_explode. First there was an inevitable outpouring of “good advice” from the same, self-styled SEO “gurus” who gave us "susanalbumparty" in the first place; then the #bubble inflated. No longer simply #used #after #every #word #in #an #online #post, or #on_websites_where_they_don’t_actually_work, or by some loser #trying_desperately_to_kick_start_a_web_meme, # started getting used in ordinary, everyday conversation by hipsters, stupid people, and marketing types trying to seem hipper or cleverer than they actually are.
It was the 2013 equivalent of air quotes from the 1990s. The #reaction when it came was captured by US comedian Jimmy Fallon and #of_all_people Justin Timberlake. LOL. The # started 2017 as a way to link conversations on Twitter and based around actual events like #WWDC or #Doctor_Who. 2013 saw the # finally bankrupted.
M is for Munchies: Normally it is pizza and coke that keep devs marching, but at Google it’s KitKats – if Google is to be believed. The search giant rolled out Android 4.4 in October and took a break from its usual confectionery based naming convention by using an actual brand name rather than a generic with KitKat.
Surely a legal minefield, with manufacturers Nestle and Hershey’s owning and operating the choc bar’s name? Apparently not, according to Google, which said all it took was a quick call to Nestle and an agreement within 48 hours that "was not a money changing hands kind of deal". Sure. Various Android fondleslab marketing tie-ups and promotions followed for lucky KitKat owners and eaters.
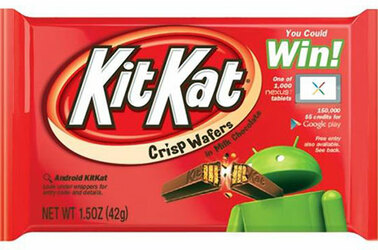
Yum - I taste a New Age, no-money brand tie-up
But KitKat when Key Lime Pie was the name in the pipeline for Android 4.4? KitKat was the Android team’s favorite snack, according to the Chocolate Factor. Oh, and relatively few people know, or have tasted, Key Lime Pie.
N is for Nefarious: While the authorities devoted their attention to snooping on us (See P is for PRISM), the real crims had been massing inside something that became known in 2013 as The Dark Web. The crims, it emerged, had co-opted TOR, a tool for internet privacy blocks your browsing and web viewing habits from outsider observers.
They were using it to conduct their activities shielded from the eyes of law enforcement and internet service providers. The case of Lostprophets singer Ian Watkins (see H is for H) raised the issue of how paedophiles had been using TOR. Code-breakers and snoops from GCHQ and NSA (see P is for PRISM) are now reported to have been instructed to “secure a foothold” in the Dark Web flushing out paedophiles, working with Microsoft, Google and Facebook in the process.
Every world has a currency and the currency of this dark world was Bitcoin. This is a peer-to-peer payment system created in 2009 by a mysterious person or group calling the Satoshi Nakomoto, the Keyser Söze of our times. It had been - and continues to be - used by 'net traders, but in 2013 interest exploded after it emerged the system’s anonymity and the fact it can be held in escrow provided the perfect cloak for drug dealers working through an online exchange called Silk Road. It was the pre-paid SIM card of 2013.
The US Drug Enforcement Agency (DEA) made their first seizure of Bitcoins – 11 worth $814.22 - in June following a raid on an alleged drug dealer’s house in South Carolina, but things peaked in October as the FBI shut down Silk Road and arrested a suspect – Ross William Ulbricht – whom they claimed to be its operator, Dread Pirate Roberts, on charges of narcotics-trafficking conspiracy, computer hacking conspiracy, money laundering and conspiracy with $3.6m worth of Bitcoin confiscated.
O is for Outsourced: A rather clever dev sent his job overseas to a subcontractor in Shenyang, China, freeing up his days to surf the web, hit various social networks and watch cat videos on YouTube. “Bob”, not his real name of course, also scored astoundingly high marks in his company’s performance reviews. The thing that gave Bob away in the end was a security audit called in by bosses who’d spotted calls from his machine to outside their VPN, and were alarmed they’d been compromised by a zero-day malware attack.
