This article is more than 1 year old
Sensors and sensibility: Quirky’s Spotter multi-purpose monitor module
Introduction to the ‘Internet of Things’ for folk scared of soldering irons
Review It sounds such a good idea: a compact, battery powered general-purpose sensor pod you can stick pretty much anywhere there’s a Wi-Fi network you have access to, and which will ping you temperature, humidity, sound, light and movement info over the internet to your smartphone.
Quirky’s Spotter: internet-connected sensor for World+Dog?
Heck, it is a great idea, and it’s one that Spotter, a joint offering from General Electric and US-based maker of crowd-voted products, Quirky, was created to realise. Think of it as an ordinary Joe’s easy-to-use introduction to the Internet of Things.
Sceptics will have already started slowly shaking their heads and muttering to themselves about fools and money being easily parted. But the Internet of Things is going to happen, and it will be products along the lines of Spotter which will take the notion of internet-connectible and remote-controllable systems to the masses.
Or, rather, it will if Spotter’s developers spend a bit more time on the software.
I wanted to try Spotter because it’s based on the Imp IoT platform developed by Electric Imp. I recently reviewed the developer version of Imp, but I wanted to see what commercial entities were making with the platform. Electric Imp makes a solder-on alternative to the developer kit’s SD card-format device, and it’s what is used here.

Spotter can run of a pair of AAs, kinda, sorta
Quirky is a website that allows punters to suggest ideas for products. Think of it as a kind of nerds’ version of Britain’s Got Talent. If a showcased product concept wins a big enough round of applause from the stalls, the concept gets made and - hopefully - stardom beckons.
Quirky’s partnership with GE is called Wink, which isn’t an abbreviation but is meant to make you think of wireless interactive connectivity. There are five products in the Wink portfolio, including Spotter, all managed through a single Wink app that’s available for free on both iOS and Android.
I tried the iOS version, but the approach is the same whichever platform you favour: run it and a wizard walks you through the process of connecting the Wink device to the app over the internet by way of your local wireless network. There’s no direct sensor-to-smartphone link - communication between the two always goes through a server.

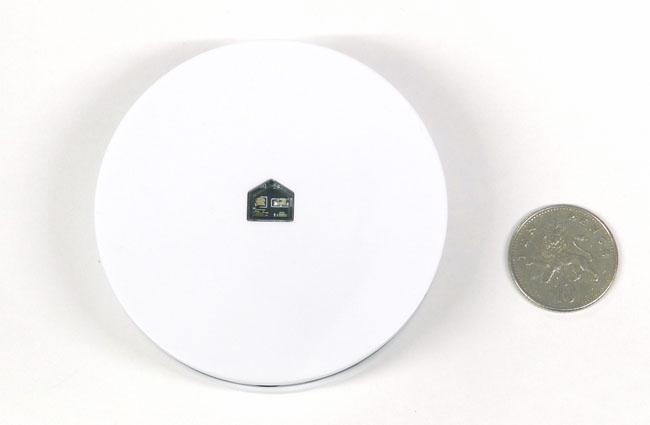
Inside, a small circuit board...
You’ll need to set up a Wink account, but that’s a trivial process and one handled within the app itself. Power on Spotter and it’s ready to be “blinked up”, what Electric Imp calls its mechanism for optically transmitting your account details and your Wi-Fi network’s configuration information from the phone’s screen to Spotter.
That done, Spotter connects to the network and then established its bona fides with the Wink server. This process went smoothly for me, but it takes only a few moments to reblink the device if it isn’t connecting. Gotchas include try to access a wireless network that’s not operating in the 2.4GHz band, moving either phone or Spotter while blinking, or not holding the two devices together during the transmission process.
The Wink app’s Spotter section has an intuitive interface that lets you define sensor values that trigger actions. Wink sensibly uses an If... then... method for defining triggers. The problem is, the range of actions is currently very limited indeed, and the number of possible trigger settings not much broader.

...which, flipped, reveals the Electric Imp module
The only light triggers available, for instance, are when it goes on or it goes off. There are no intensity level triggers. The only actions either of these events can be used to initiate are to present a notification on the phone or to send an email.
