This article is more than 1 year old
NASA pic: DOOMED ice Comet ISON literally had snowball's chance in hell
Close encounters of the burned kind
Photo NASA reckons only a little bit of plucky Comet ISON survived a close encounter with the Sun – and judging by this space photo, we're not surprised.
After reaching its perihelion during Thanksgiving, the iceball failed to reappear, at least according to the agency's Solar Dynamics Observatory, which captured the portion of space where the comet was supposed to be, marked here with a cross:
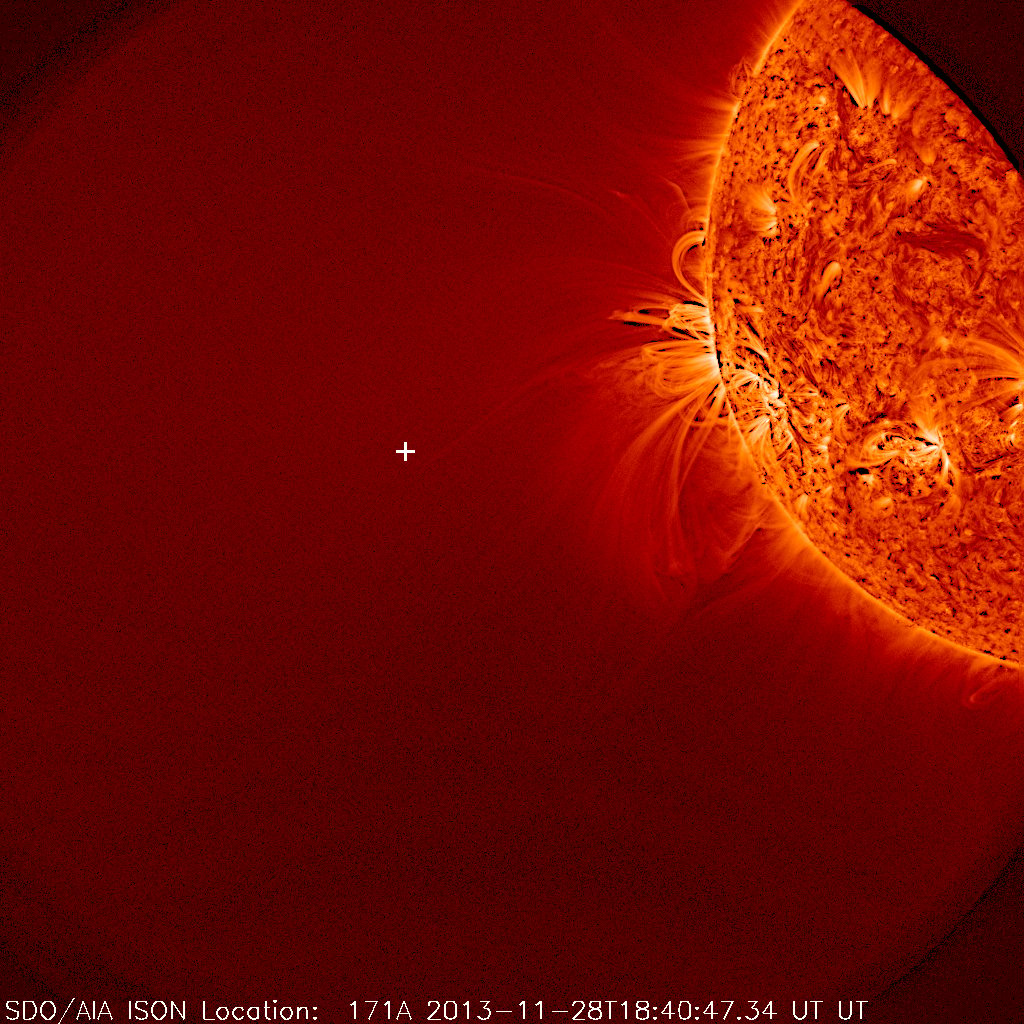
+ marks the spot where ISON was supposed to soar past mighty Sol's hellish grasp
Click to enlarge NASA/SDO's snap
However, subsequent images from the Solar and Heliospheric Observatory show that perhaps a reduced nucleus is intact and spewing out material.
NASA notes: "The question remains whether it is merely debris from the comet, or if some portion of the comet's nucleus survived, but late-night analysis from scientists with NASA's Comet ISON Observing Campaign suggest that there is at least a small nucleus intact." ®
