This article is more than 1 year old
BIG IRON cluster warriors put pedal to HOT METAL
We node you like those accelerators
HPC blog We saw an interesting assortment of gear from the teams competing in the SC13 Standard (Big Iron) Track of the Student Cluster Competition.
As you can see on the handy table below, the teams had a lot in common on the surface. They all ran some variety of Intel Xeon as their base CPU, most were using Mellanox Infiniband interconnects, and every team had some sort of accelerator or co-processor.
But there are plenty of differences as well. The Australian iVEC and the Chinese NUDT teams, for example, took a 'more nodes is more better' approach, sporting eight nodes each. The Aussies also went for an interesting node strategy, with all 8 of their accelerators located on only two nodes.
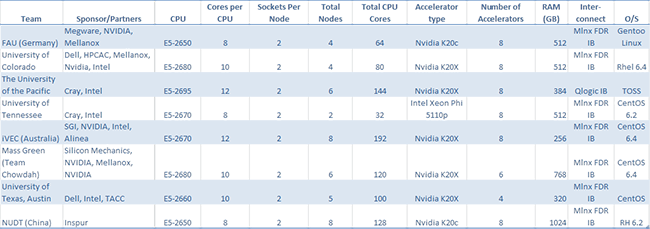
You'll also notice that almost all of the teams went in for accelerators in a big way, festooning their clusters with either 8 NVIDIA Keplers or 8 Intel Phi co-processors. Team Longhorn (Texas) took what they call a more balanced approach with only four GPU accelerators.
Using this many accelerators can be somewhat risky. While they can add a whole lot more processing power, they can only do so on applications that are optimised to use them efficiently.
The problem for competitors is that SCC rules do not allow teams to power down or physically remove any component after the start of the bout. So if you have an app (or apps) that don't efficiently use your accelerators, you can't do much beyond idling them to reduce the drain on your power. And even at idle, having a bunch of these things can really take a chunk out of your 26 amp/115 volt power allowance.
In upcoming stories and video blogs, we'll take a closer look at each team, their gear, and their rationale for making the decisions they made. We'll also give you an idea of how the competition proceeded day by day and, of course, cover the first Pro-Am Celebrity Cluster Challenge. (Which sucked up a huge amount of my time, since I was the organiser and ultimate arbiter of the Pro-Am. It was fun, but fraught with challenges. Stay tuned for more.) ®
