This article is more than 1 year old
Your kids' chances of becoming programmers? ZERO
We had it all in the 1980s. Here's what went wrong...

The 'stupidly expensive' RM (Research Machines) 380Z
Z80 crew vs BBC Micro goody-goodies: This means war
A flipside of our passion was identifying ourselves with the tech we used and there was no love lost between the Z80 gang centred around the ZX80, ZX81 and ZX Spectrum and our sworn enemies the 6502 BBC Micro goody-goodies (and later the Oric) and for the rich kids, the Apple II.
We were clearly winning; the numbers spoke for themselves. The higher cost of the Beeb put it out of the reach of most of us and since we were trying to think of things we could sell, the market was clearly better. Of course that success was causing problems as the wave of Spectrum games both made it more popular and drew many away from even pretending to code.
So the BASIC reason we wrote code was that we couldn’t buy it and even stealing programs was really very hard. So ironically the utter uselessness of the BBC, Sinclair, Dragon, Oric et al meant that for years we were driven to coding to make the damned computer actually do something, anything. At Campus London last month that nice Mr Osbourne informed me that he was a fellow ZX81 veteran at his rather posher school computer club – which he presumably upgraded to the VBA macros with which he runs the UK economy. No education is ever wasted is it?
Chaos in Computer Clubs
So then like now, real programming was done outside lessons in computer clubs of variable legitimacy. In my school, like most others, the teachers had neither the time nor the expertise to supervise these. So long as the complaints about our activities stayed within certain bounds, we were left to get on with it.
The current ICT syllabus is designed on the basis of inclusiveness, dumbed down so that any child can learn it and so that ICT can be taught by someone with no qualification in the subject. That was not the way my computer club – or most of the others that people have told me about – worked. Like many '80s geeks, I got a real kick out of explaining the mysteries to lesser kids, but if they failed to understand, then they either drifted off, or had the piss taken out of them until they got the message.
In retrospect that wasn’t ideal, nor was the fact that the pushing and shoving to get time on the terminal or the stupidly expensive Research Machines system (RM 380Z) was just a bit too Darwinian. However it did mean that only those who had some sort of talent pursued it further, again in contrast with today.
I have spoken with profs at Russell group universities (the top 11 in the UK) and they share that in 2013 some kids turn up not only having never programmed, but under the bizarre delusion that they don’t need to.
As you read this, first-year CompSci grads at Cambridge – which is believed by some to be a good uni – are starting to be taught with the assumption that they know no programming: an assumption that ought not to have lasted long after my cohort in 1981.
Hack or Die
Back then a kilobyte was a huge resource, forcing us to develop all sorts of hacks to get the most out of memory. We had to use ingenuity mixed with bloody-mindedness, using video memory to store program state; single byte offsets rather than 16-bit pointers; writing over memory that had stored program code that was no longer needed; string folding; and, for the more adventurous, machine code. In many BASICs, long variable names consumed too much memory and few of us paid that much attention to comments or structure.
To code anything interesting, we had to know our machines from top to bottom. Personal Computer World as well a sudden horde of computer mags in the 1980s published “how to” pieces that went right down to the metal. For us there was no concept of hardware abstraction or portability. We felt pretty smug when it worked on the box in front of us and since the 8-bit micros were so different, especially in their BASICs, only generic machine code for things like moving blocks of memory or for doing calculations had any chance of working on multiple systems.
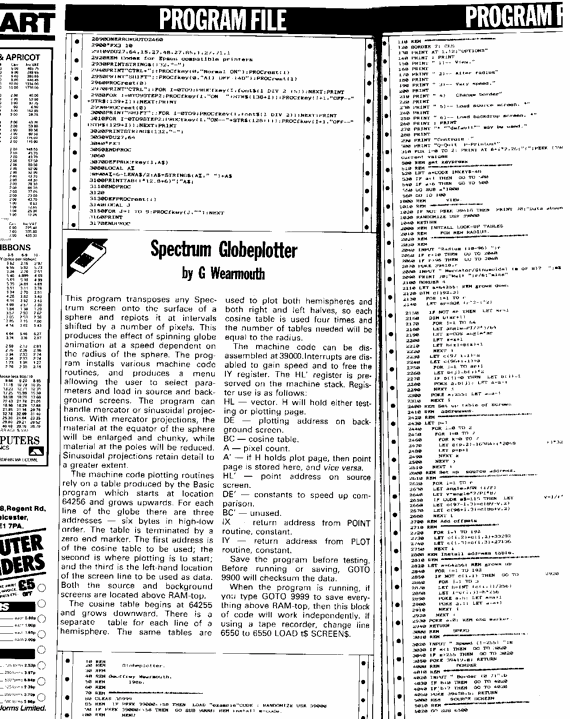
Listings from PCW.
This has led to a fallacy of programming management that making the developers use underpowered machines makes them write tighter code, when in fact we both know that just means we take longer to turn out the same junk. Was the Spectrum better than Visual Studio? The VB environment I use on my kids wasn’t even sci-fi back then, having vast arrays of functionality, syntax assistance and – despite the best efforts of the one part-timer who works in MS documentation – the online help is still useful.
VB.NET, Java, C++, Delphi etc are all big languages with big libraries, making it a waste of time to write your own string-handling or graphics routines. Knowing the name of the right function has become more important than understanding how it works. Own up, could you code DDI or Bresenham’s algorithm without looking them up? How many algos do you actually know? Is that even relevant to your work?
BASIC is still with us. When IBM launched the PC, there was no question that it might not have BASIC in ROM built into the computer itself. And it is still the best way to macro program Microsoft apps – except of course on the wretched Surface RT. It is not a coincidence that the MS platform that has performed the most poorly is the one that denied corporates the use of VBA in order to make them buy one of the eight actually useful apps in its app store.
IBM's PC came with Mortgage.BAS, a badly written demo app in awful BASIC. By the time I was working on OS/2 at the end of the 1980s, this had been consigned to the dustbin of history. Which was a big mistake, as it turned out that some banks were using it in real life and all sorts of kludges had to be made. Visual Basic was also part of the reason MS beat IBM in the O/S wars. We BASIC hackers were too many to be resisted.
So by the mid-1980s, programming in schools was surging, parents raised money to buy kit for their schools, Research Machines weren’t yet in a position to stop kids writing code and CompSci grads like me were coming out of university in enough numbers that properly qualified teachers should no longer be a rarity.
That’s not the world we observe now, though, is it?
In part 2, I will explain why. ®
