This article is more than 1 year old
NSA, UK hacked Yahoo! and Google data center interconnects – report
Project MUSCULAR taps millions of YOUR records a month
British and US intelligence agencies managed to tap into the connections between data centers run by Yahoo! and Google, and in one month this year slurped 181,280,466 records, including metadata and the contents of communications, according to new documents from Edward Snowden.
A report dated January 9, 2013, from NSA’s acquisitions directorate, detailed the operation, dubbed MUSCULAR, in which operatives from the NSA and Britain's GCHQ tapped the fiber-optic transmission cables from the non-US data centers run by the two firms.
One document, sent to the Washington Post, shows a hand-drawn diagram of how it's done, including a smiley face.
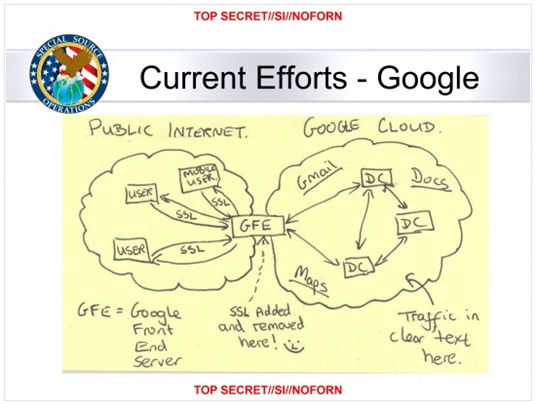
NSA surveillance design and emoticon
“We have long been concerned about the possibility of this kind of snooping, which is why we have continued to extend encryption across more and more Google services and links, especially the links in the slide," Google’s chief legal officer, David Drummond, told the paper in a statement.
"We do not provide any government, including the US government, with access to our systems. We are outraged at the lengths to which the government seems to have gone to intercept data from our private fiber networks, and it underscores the need for urgent reform.”
Under the scheme, GCHQ intercepts the traffic and stores it in a "buffer" that can hold between three and five days' worth of traffic from the data centers. The NSA then picks through this to find useful information using up to 100,000 search terms before emptying the buffer.
What makes MUSCULAR so puzzling is that under the terms of the PRISM program, US intelligence services already have access to the records of both Google and Yahoo! Either Snowden's documents are incorrect or the NSA and GCHQ have decided to cut out the middle man and go for the data directly.
The Washington Post speculates that the reason overseas data centers are targeted is to avoid the possibility of collecting data on US citizens in breach of America's Foreign Intelligence Surveillance Act. In a statement the NSA denied this, and claims that it gathered "vast quantities of U.S. persons’ data from this type of collection."
"NSA applies Attorney General-approved processes to protect the privacy of U.S. persons - minimizing the likelihood of their information in our targeting, collection, processing, exploitation, retention, and dissemination," it said. "NSA is a foreign intelligence agency. And we’re focused on discovering and developing intelligence about valid foreign intelligence targets only.”
The NSA is subject to political oversight and on Tuesday intelligence operatives testified in front of Congress, along with those tasked with conducting a review of surveillance activities by the NSA and others. Representative Mike Rogers, who as head of the Permanent Select Committee on Intelligence helps provide congressional oversight of the NSA, shared this little gem with the panel.
"You can't have your privacy violated if you don’t know your privacy is violated, right?" ®
