This article is more than 1 year old
Reply-all email lightning storm STRIKES TWICE at Cisco
MILLIONS of time-wasting messages bounce around network giant
Cisco is tackling another email storm today, just weeks after its servers were deluged with millions of "reply-all" messages being sent by the networking giant's staff - with many requesting they be removed from the list.
The Register has heard from Cisco workers who are currently in the, er, eye of the storm, which is apparently even bigger than the last one to hit the company, back in September.
Others have taken to Twitter to moan about the latest reply-all emails to jam up their work accounts.
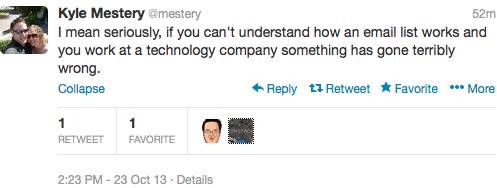
As Cisco's principal cloud engineer Kyle Mestery noted: "Nothing like a massive, completely unnecessary email storm on a Wednesday morning. Is email really this hard for people to use?"
He added:
Cisco could not be reached for comment at time of writing. Readers may recall it was a little shy about responding to our last story when the firm's previous email storm struck.
El Reg is trying to corroborate claims that the latest "reply-all" email to have crippled productivity at Cisco was sent out to a whopping 34,562 employees at the company.
Just as night follows day, some of those staffers committed the mortal sin of hitting reply all to the reply-all message requesting to be removed from the list.
Other staffers than piled in by berating the "idiots" who failed to realise they were creating yet another email storm.
It's unclear - given the last costly fiasco that was estimated at $600,000 - why Cisco's sysadmins hadn't learned from their mistakes by applying a restricted senders' list to prevent chaotic, productivity-sucking reply-all emails from being sent.
Naturally, El Reg is seeking an answer to that question.
Do you work at Cisco? Are you tired of email storms? Want to talk to us in confidence about the latest saga? Then get in touch – click the author's name at the top of this story. ®
