This article is more than 1 year old
Bigger, fiddly to manage: The second coming of Windows Server 2012
Microsoft's R2 unit automates but frustrates
Blink my hurting eyes, behold Linux
Linux integration is improved with dynamic memory and backup from the host, provided the latest integration services are in the kernel.
My generation
Finally, the most forward-looking new feature is Generation 2 VMs. Why emulate legacy hardware, the argument goes, if you are going to run a modern operating system? Generation 2 VMs have no emulated IDE controller, PCI bus or legacy BIOS or network cards. Instead, they have UEFI bios, enabling secure boot, virtual SCSI, VMBus and synthetic network controllers, which means optimisation for the Hyper-V environment. Only Windows Server 2012 or higher, or 64-bit Windows 8 or higher, are supported as guest operating systems.
Powershell
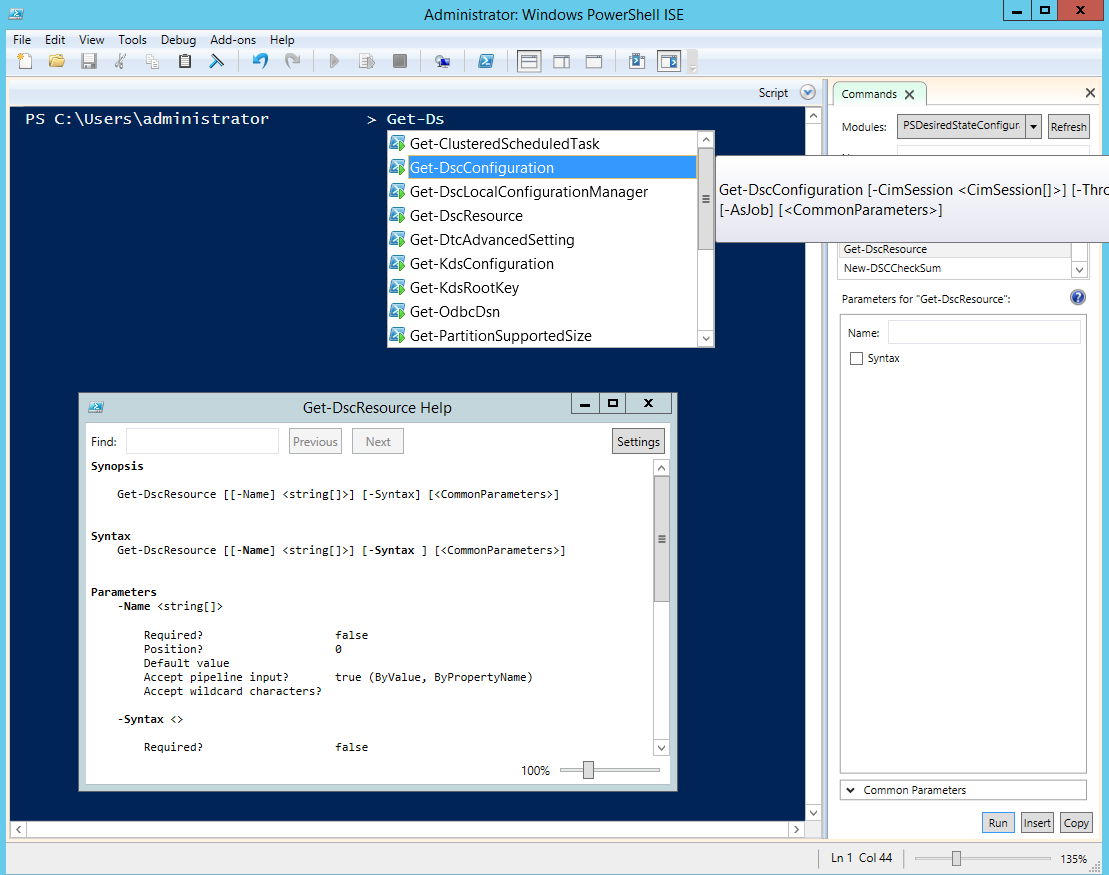
PowerShell, Microsoft’s scripting and automation engine, is becoming the primary tool for managing and configuring Windows Server. Walking through Microsoft’s example deployments you dip between GUI tools and PowerShell commands. Some things can only be configured through PowerShell and that is by design. Server 2012 R2 introduces PowerShell 4.0, which has a ton of bug-fixes and minor improvements, and one big new feature, Desired State Configuration (DSC).
The idea of DSC is that you can define the state of a Windows Server instance in code, using configuration blocks to specify what is installed and how to define, say, registry keys entries. You can also create files, run setup routines, add and remove Windows features, and so on. A DSC script is idempotent, which means it can safely be run multiple times.
Defining the state of a server in code has huge potential. You can imagine, for example, applications that have all their deployment requirements coded and versioned in the same way as the rest of their code. DSC depends on providers though, and these are limited to essential Windows features for now.
Opscode, the company behind a configuration automation tool called Chef, is working on using DSC to improve Chef support for Windows.
DSC is promising but needs more providers, third-party support and example scripts to realise its potential.
Bring your own device
If virtualisation is the number-one effort in Server 2012 R2, then support for Bring Your Own Device (BYOD) must be number two. The goal looks something like this. Users can register their PC or gadget for workplace use, giving them access to a company portal for installation of corporate apps. Company documents are available in work folders on the device, and they also have access to Windows desktops and applications via Remote Desktop Protocol (RDP).
Single sign-on avoids repeated authentication, but multi-factor authentication is supported where needed. Documents may be encrypted. If the user leaves the company, or the device is stolen, selective remote wipe removes corporate apps and data. Administrators manage everything through System Center Configuration Manager.
Sounds good, but there are a lot of moving parts here, some of which do not yet work smoothly or are not quite done. The pieces include Windows InTune, which is a cloud service for mobile device management; Active Directory supplemented by Active Directory Federation Services (ADFS); Windows Server file services; Remote Desktop Services; Information Rights Management; and System Center to provide an integrated management console.
New in Server 2012 R2 is Workplace Join, also called Device Registration, which allows users to register devices in Active Directory. This installs a certificate on the device and enables single sign-on via ADFS. Windows (including Windows RT for Microsoft’s ARM-based tablets) and iOS devices are supported with Android support to follow. New in System Center 2012 R2 is the ability for Configuration Manager to link to InTune to provide a single management console for PCs and devices.
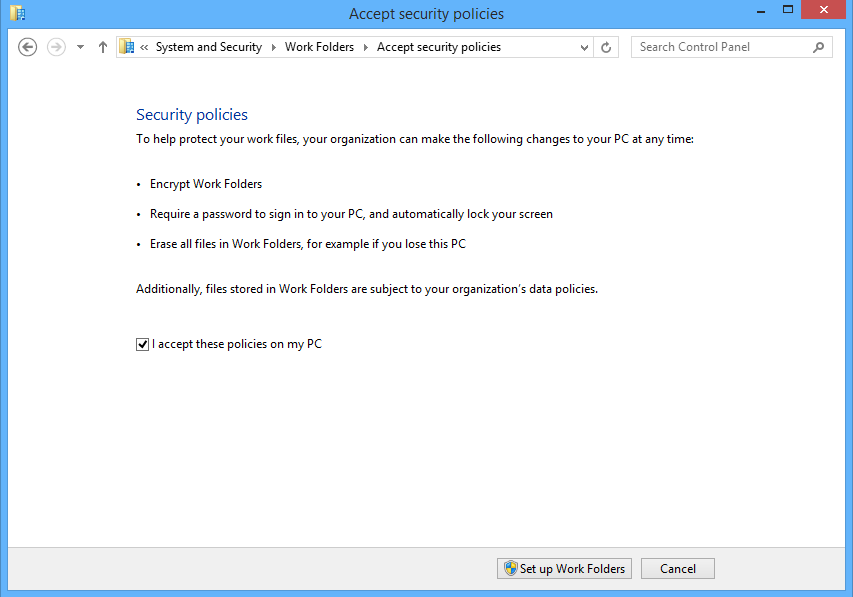
Work Folders, which publishes a user document folder so that a synchronised copy appears on their PC and device, is also a new feature. Currently only Windows 8.1 clients are supported, including Windows RT, but support is promised for other platforms. Work Folders is a new feature of File and Storage Services in Windows Server, and can be accessed remotely without a VPN.
Microsoft handed press attendees at a Server 2012 R2 workshop Windows RT devices running the released-to-manufacturers version of Windows 8.1 RT, allowing hacks to try out the kit. After successfully turning on Workplace Join and Device Management, you can run the Company Portal app. You run the app and a login dialog appears. You enter your username, then rather than letting you enter a password, the app redirects you to a second log-in where you have to enter your username all over again, following which sometimes the company portal eventually appears, and sometimes you get an error and have to try again.
Work Folders raise the question of why Microsoft has introduced yet another technology for file sync, joining offline files (a feature of Windows Server for years), SkyDrive Pro that works with SharePoint and is an evolution of Ray Ozzie’s Groove, and not to mention the consumer SkyDrive or abandoned technologies like Live Mesh. The advantage of Work Folders is forthcoming device support and, I suppose, the fact that it does not need SharePoint.
RDP on devices, on the other hand, works well, even over the internet, probably because it is based on mature technology.