This article is more than 1 year old
Volvo: Need a new car battery? Replace the doors and roof
Super capacitor sandwich built into body panels
Volvo reckons it has a better place to locate an e-car’s power storage: in the vehicle’s body panels.
The technique throws out traditional lithium-based batteries in favour of a carbon fibre and polymer resin sandwich. What Volvo, boffins from Imperial College and researchers from seven battery and materials companies together call “a very advanced nanomaterial” is embedded in the resin, which is sealed in between two layers of carbon fibre to form a “super capacitor”.
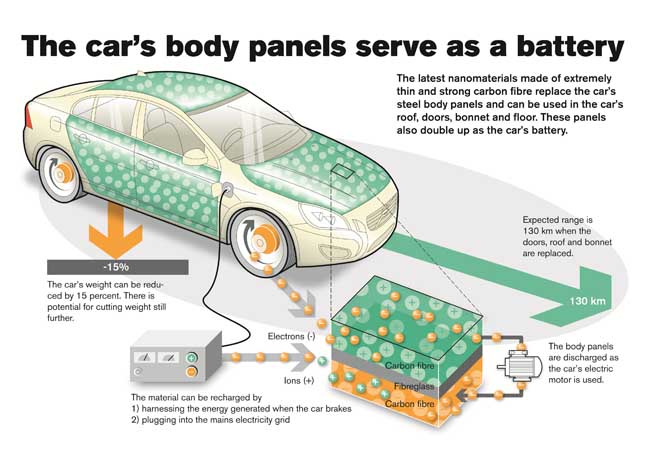
Using carbon fibre means the units can be formed into car body panels: doors, roof and bonnet. As such, they replace the steel panels used today, reducing the car’s weight by up to 15 per cent - more since the car then doesn’t need a bulky lithium battery.
The very large size and weight of e-car batteries are the key limitations on the vehicles’ range and performance.
The new material is charged using brake energy regeneration. Or you can plug it into the mains, of course.
Volvo, of course, has yet to build a test car equipped in such a fashion, though it has made a couple of test panels - boot and bonnet - on one of its S80s with which to evaluate the technology.

The carbon-fibre boot battery
It believes the boot panel alone has the potential to replace a standard lead-acid car battery, while the bonnet panel is also “powerful enough to supply energy to the car’s 12V system” and stand in for the S80’s stop-start battery, and is sufficiently rigid to replace the rally bar.
Volvo said this week that tests “showed that this material not only charges and stores faster than conventional batteries can”.
The car maker also claimed the process was “cost-effective”, though it hasn’t detailed how much this “concept” costs to make and install - or when it might introduce the technology into cars it can sell.
More to the point, perhaps, it didn’t discuss the safety implications of placing the power storage system in the car parts most likely to be damaged during collisions. ®
