This article is more than 1 year old
Boffins offer ROUTER DEATHLIST for software-defined network builders
You didn't think SDN would mean no upgrades, did you?
Unless you've got fathomless pockets, a scary aspect of a software-defined networking implementation is the necessity for an infrastructure upgrade, since nobody wants to forklift every router in a big network all at once. Now, a paper co-authored by Nokia Siemens Networks' Marco Hoffmann proposes a set of algorithms to help plan the rollout.
The aim of the paper, published at Arxiv here, is to create a methodology that takes into account the current state of a network, balancing gains from traffic engineering with limitations on capital expenditure. Perhaps obviously, the authors say that “the sequence of migration plays a vital role, especially in the early stages of network migration to SDN”.
The group, which includes three authors from the Technical University at Braunschweig (Tamal Das, Marcel Caria and Admela Jukan), took on the system architect's perennial question: “if there's got to be an upgrade, which kit do I nuke first?”
As the paper puts it, in more academic terms: “operators need to understand how their network can make best use of traffic engineering capabilities enabled by SDN, during various stages of a migration process.”
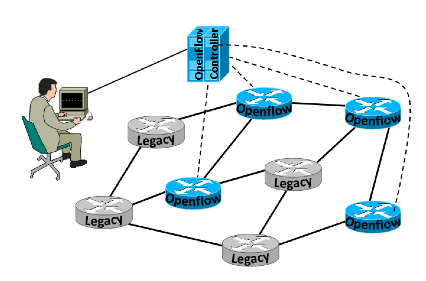
Some of your routers get migrated first - but
which ones? Image source: arxiv.org/pdf/1310.0216v1.pdf
To try and answer this question, the researchers produced algorithms designed to assess two constraint cases: the network operator is limited either by the number of routers that can be migrated in a single step, or is limited by the available capex at any given moment (these cases look identical, but they aren't quite, since in the first case, the time it takes to drop in a new router is a more important constraint than the money needed to buy it).
The process starts with a path analysis to identify key nodes that must be SDN-enabled if a path is to be used for traffic engineering. For these paths, the paper presents “greedy algorithms” that test different migration scenarios for maximum performance gains under the different migration constraints. ®
