27
This article is more than 1 year old
DRAMA at 75,000 FEET: Our Playmonaut's TERROR PLUNGE from EDGE of SPACE
Plucky Reg operative finally found in remote valley
Fortunately no Fossett-style fate for Playmonaut No. 2
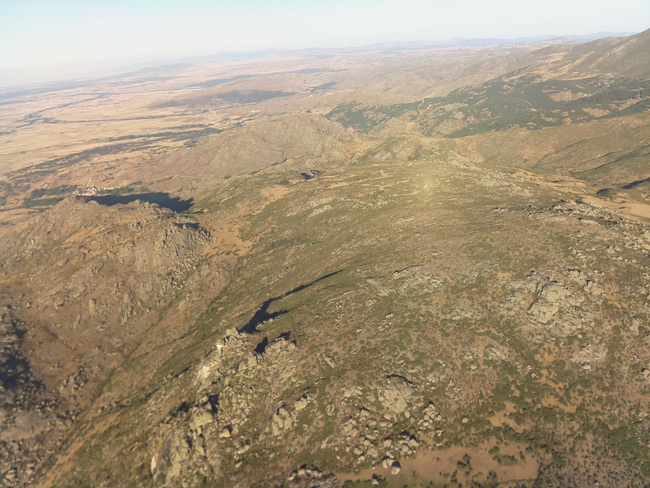
...we arrived at a ridge overlooking the valley in which our playmonaut had spend the night:

After a 1km trek...

... we walked right up to the payload:


Our diminutive 'naut was shaken but otherwise well. The CHAV had hit the ground with a hell of a bang, but the nose had absorbed the impact:

Here are two remarkable images from the aircraft's nose mounted Raspberry Pi camera, before the ground rushed up to meet it: