This article is more than 1 year old
NASA plots Chelyabinsk plume
11,000 tonne asteroid's dusty debris went around the world in four days
Video Not only did the Chelyabinsk bolide explosion send shock waves around the world. It also sent a plume of dust, and for the first time, such a plume has been observed by space-borne instruments.
The data, captured by the Suomi NPP satellite's Ozone Mapping and Profiler Suite (OMPS) of instruments, gave the agency a rare chance to test its modelling capability against what amounted to a natural experiment. Not only could it test the accuracy of some atmospheric models, it also got the chance to see how well OMPS could detect and track meteor dust.
From the OMPS observations, NASA says, it was able to generate models predicting how the plume created by the asteroid's 30-times-Hiroshema-sized explosion would travel – and test those predictions against later observations.
And there were some surprises in how the plume from the 11,000-tonne asteroid spread and stretched over time. Surprise number one was that the plume reached so high – well into the stratosphere, which usually caps how high airborne aerosols can reach. Another was how coherent the plume remained, since as NASA notes, high-altitude Northern Hemisphere winter winds are usually far less consistent than those experienced by the Chelyabinsk plume.
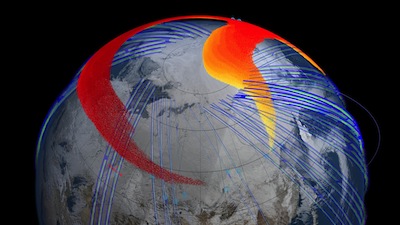
In just four days, the fastest parts of the plume (red)
had circled the globe. Image: NASA
In this release, NASA's Nick Gorkavyi says “we saw the formation of a new dust belt in Earth's stratosphere, and achieved the first space-based observation of the long-term evolution of a bolide plume."
In this animation, NASA explains that it only took four days for the plume to circle the globe.
By 3.5 hours after the explosion, which is when the satellite made its first pass over the site since the blast, some the plume had already reach 40 km altitude. At high altitude the bolide dust was screaming away from the site at 300 km/h, while closer to the ground, the dust was heading eastwards at a much more sedate 75 km/h.
NASA notes that there was detectable dust three months after the explosion. ®
