This article is more than 1 year old
Java devs warned of pushbutton exploit for buggy Struts framework
When they said you should upgrade, they meant it
Java developers were warned, but they didn't listen. Security researchers at Trend Micro report that old and vulnerable versions of the Apache Struts framework for Java are still in widespread use, and now Chinese hackers are using automated tools to exploit their flaws.
The vulnerabilities in question were patched in the July Struts release, according to a blog post by Trend Micro senior threat researcher Noriaki Hayashi. But many applications are still running on older, buggy versions that can allow attackers to execute arbitrary code.
The exploits are made all the easier by a new tool developed by Chinese hackers, which makes executing certain commands on vulnerable remote servers as easy as pushing a button.
With a few simple clicks, attackers can determine the name of the current user account, display the version number of the OS, view network and system configuration information, list the contents of directories, and – particularly worryingly – add new user accounts.
The tool also reportedly includes a "WebShell" feature that makes it easy to plant a backdoor into vulnerable servers. Once this is done, the hackers can execute arbitrary commands from their keyboards using only a web browser.
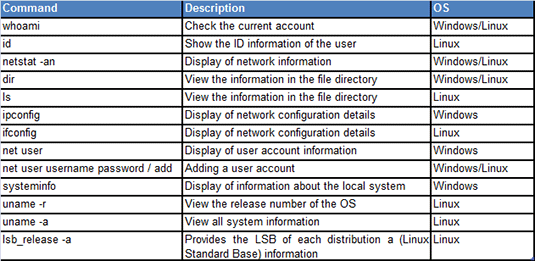
Here's what attackers can do on your Struts server using a Chinese script-kiddie tool
The attack works on servers running either Windows or Linux, although the actual commands that can be executed will differ depending on the OS.
Trend Micro is hardly the first company to warn developers of vulnerabilities in open source frameworks and the dangers of running old versions. In March, a study by Sonatype and Aspect Security found that developers downloaded out-of-date versions of the most popular frameworks 33 per cent of the time, even though newer versions with security fixes were available.
Among the top Java frameworks, Struts is also a particular target for malicious hackers. A January report by CAST found that applications built using Struts were highly likely to be misconfigured, and they delivered the lowest code quality scores overall.
Of course, the tendency to stick with outdated versions of Java frameworks is somewhat understandable. Frameworks like Struts often power highly complex, mission-critical applications that require rigorous testing before any changes can be deployed.
Security patches can also sometimes break apps when vulnerable features are removed. But with flaws as severe as the ones now being exploited in Struts, it's essential that Java development shops stay on the ball and migrate to secure versions ASAP.
In this case, blocking the Chinese automated exploit tool requires an upgrade to Struts 2.13.15.1 – which was released in July – or to any later version. ®
