This article is more than 1 year old
Google study finds users ignore Chrome security warnings
Research tracks 25m browser warning messages, says Chrome users most reckless
You're surfing the 'net when Chrome decides not to bring you the web site of your choice, but instead a page warning that the site you'd hoped to visit might be bogus or contain malware.
Do you:
(a) Click on “Proceed anyway” because you really want to see the cat picture someone Tweeted to you; (b) Click “Back to safety” because it's not worth having crims empty your bank account for a peek at one cute kitty.
If you picked the first option and ended up being pwned by something nasty, there's no need to feel completely stupid: a new study by Google has found that over 70 per cent of people ignore some such warnings.
The study, Alice in Warningland: A Large-Scale Field Study of Browser Security Warning Effectiveness ((PDF) collected “25,405,944 warning impressions in Google Chrome and Mozilla Firefox in May and June 2013” and found that plenty were ignored.
Here's the basic data.
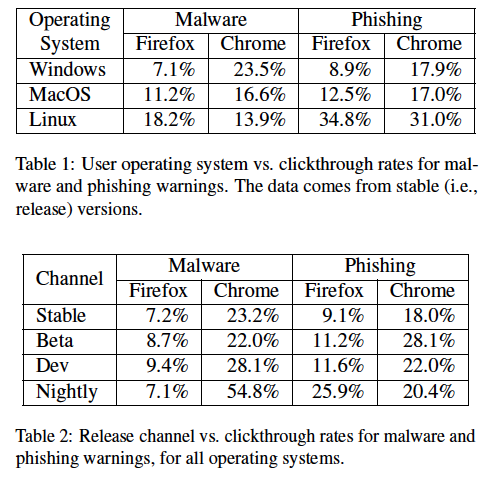
Interestingly, users are less circumspect when using early versions of software, as this block of data reveals.
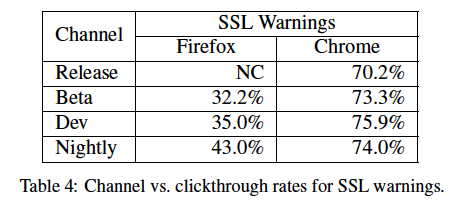
Keen-eyed Reg readers have probably noticed the table above also shows Chrome users ignoring more warnings than most.
The study's authors, one Googler and Devdatta Akhawe of the University of California, Berkeley, are not sure why Chrome users are so blasé. False positives are one possible reason, differing levels of competence among users are also found to account for another point or two of difference. “Warning fatigue” is advanced as another reason users ignore warnings, and the study re-learns one of the lessons of Windows Vista by pondering if fewer warnings may be one way to improve security.
“Our findings motivate more work on browser security warnings, with particular attention paid to demographics,” the paper concludes. “At Google, we have begun experimenting with new warning designs to further improve our warnings.” ®
