This article is more than 1 year old
Amazon button leaked user traffic
Shopping button let sneaks snoop
Amazon is the latest company to come under fire for misusing its browser extension bar, with security researcher Krzysztof Kotowicz accusing the company of invading privacy via its 1Button extension for Chrome.
The blogger, in a post entitled Jealous of PRISM? Use "Amazon 1 Button" Chrome extension to sniff all HTTPS websites! says 1Button not only provides a side-channel attack for SSL encrypted data on user machines: it sends some user Web activity information over plain text.
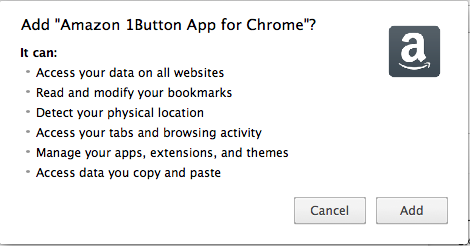
And even worse: as he points out, if you're a 1Button for Chrome user, you've given the extension permission to do all of this stuff.
Kotowicz's accusations are extensive and specific. He says the Chrome extension:
- Reports URLs users visit to Amazon (using HTTPS);
- Attaches an external script (currently harmless) to Websites users visit;
- Reports the content of some Websites users visit back to Alexa – including Google searches over HTTPS and some search results.
It's this last that Kotowicz describes as “evil”: URLs and extracted page information travelled to widgets.alexa.com as plain text over HTTP.
Then there's the configuration files. As Kotowicz writes: “upon installation (and then periodically) [the 1Button extension] requests and processes two config files.
“[The] first file defines what HTTPS sites can be inspected. The second file defines URL patterns to watch for, and XPath expressions to extract content being reported back to Alexa. The files are fetched from these URLs:
- http://www.amazon.com/gp/bit/toolbar/3.0/toolbar/httpsdatalist.dat
- http://www.amazon.com/gp/bit/toolbar/3.0/toolbar/search_conf.js
“Yes. The configuration for reporting extremely private data is sent over plaintext HTTP. WTF, Amazon?”
He posted exploit code at github, an action was sufficient to persuade Amazon to repair one flaw: data is now sent over HTTPS instead of HTTP.
Check your permissions: why would you click 'yes'?
However, extent of the data captured by the button suggests it's far more invasive than is necessary for a shopping button. ®
