This article is more than 1 year old
What it was like to grow up around the world's first digital computers
And build slot machines out of the spare bits
Centenary Ever dreamed of taking Saturday morning trips to the computer lab at Cambridge University, playing with the equipment, cannibalizing old computers, and building new machines from the bits?
We're not talking metal Meccano minnows run on AA batteries, either. We’re talking actual, operating electro-mechanical machines powered by mains electricity and built using the unwanted bits of your dad's decommissioned computers. If your dad is Sir Maurice Wilkes, that is.
How the volunteers at The National Museum of Computing (TNMOC) painstakingly rebuilding one of Wilkes’ most famous old computers, EDSAC, from scraps of memories and old photos, must shake their heads at the way Wilkes’ old machines were thrown aside.
“Yes, we're all very conscious of computers – we were a computer family,” Sir Maurice’s son Anthony recalls during an interview with The Reg. He tells us of how he and his sisters Margaret and Helen had the run of the Cambridge lab and got access to some very historically valuable equipment.
Family man and geek dad is the other side to the story of Sir Maurice, the architect of EDSAC – the world’s first general purpose digital computer and basis of the world's first business computer, LEO.
Mathematician, physicist and award-winning computer engineer – yes. The man who had EDSAC operational in 1949, EDSAC 2 in 1958 and Titan in 1964 earned major awards for his work - the The Kyoto Prize in 1992 for advanced technology and the Turing Award in 1967 among them. We know these facts.
But a geek dad before the term even existed? It’s a revealing insight into the man, and one that shows just how deep Wilkes’ obsessions and interests ran.
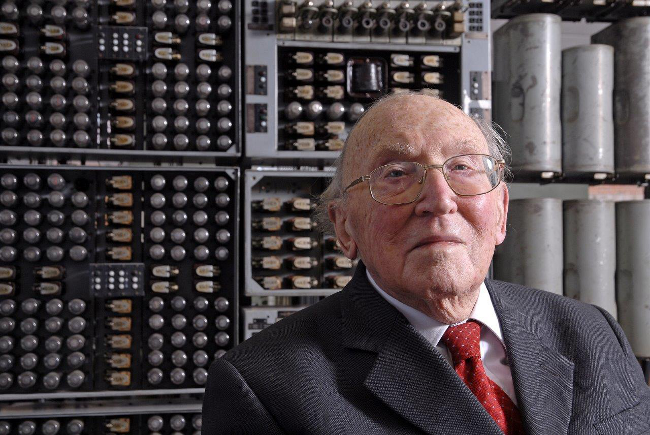
Scientist, computer pioneer, geek dad: Sir Maurice Wilkes, photo: TNMOC
Wilkes also ran Cambridge University’s famed computer laboratory from 1945 to 1980. He did so with a singular tightness, setting the vision with one hand firmly controlling direction; but he was no authoritarian. Rather, the picture that emerges is of a people person with a gift for working with others.
Wilkes, who would have been 100 on June 26, first made his mark on the wider world with EDSAC. The dons of Cambridge had wanted a bureau running computers that performed services for the teachers and students. When it came to giving Wilkes the job, they’d picked the right man.
He built EDSAC as a no-nonsense, practical computer - not some research machine built to prove a theory.
Anthony tells us: “It [EDSAC] was designed to provide a service to other scientists in the university. All the other computers were experimental. But the EDSAC had many regular users. They used to queue up with their paper tapes. This was as far as I am aware the only place in the world at that time one could go to actually use a computer.”
TNMOC director David Hartley had Wilkes as his research director and worked with Wilkes building EDSAC’s successor Titan during the 1960s. Hartley told us of Wilkes on EDSAC:
“His objective was not to build a computer but build a computing service, but had to build a service he needed a computer. That contrasted with other computer adventures.”
Wilkes tapped two of the newest technologies in computing. One of these was vacuum tubes, or thermionic valves, that turned computers from mechanical to electronic devices by directing the flow of current. Vacuum tubes were getting picked up in other computers in the 1930s and 1940s.
The other new technology was mercury delay lines for memory, converting a bit from an electrical to a sonic pulse transmitted through a tube of liquid mercury. The concept was developed by American engineer John Presper Ecker, borrowing from radar. Ecker co-designed the Electronic Numerical Integrator Computer (ENIAC) that used both mercury delay lines and valves when it went fully operational in 1949.
He reminds us of an early Steve Jobs who reputedly had the concept for the iPad years before the technologies in chip, screen, touch and battery became realities.
