This article is more than 1 year old
Energy sector under increasing attack: DHS
SQL injection, phishing, watering holes – the usual
The Department of Homeland Security, via its ICS-CERT group, is reporting growing attacks against critical infrastructure with the energy sector leading the way.
Its most recent ICS-CERT Monitor report states that of more than 200 incidents it investigated between October 2012 and May 2013, 53 percent were in the energy sector. This far outstripped attempts to attack “critical manufacturing” facilities at 17 percent, while the transport and communications sectors could only manage to attract 5 percent of attacks each.
It states that the most common attack vectors were watering hole attacks, SQL injection, and spear-phishing attacks.
The 200-plus incidents in six months represents a dramatic increase compared to the 198 incidents reported to ICS-CERT for the whole of 2012. However, this could reflect a greater willingness to report incidents, in addition to a growth in attacks.
The report notes that on five occasions, the ICS-CERT decided to deploy its onsite teams to analyse the victim's systems and network, three times to energy sector companies and twice to manufacturers.
ICS-CERT complains that its onsite investigations were hampered by “limited or non-existent logging and forensics data” from the target network. ®
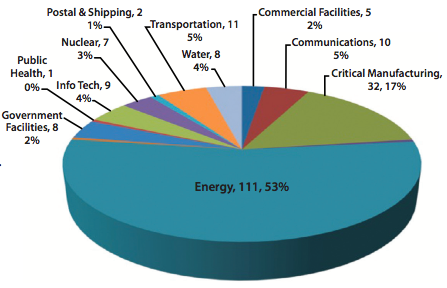
Energy sector the leading light in network attacks.
Source: ICS-Cert Monitor
