This article is more than 1 year old
AT&T patents P2P content tracking system
System and method for snooping on torrents
AT&T says it has developed the ability to accurately track content being shared by P2P file-sharing networks like BitTorrent, and has received a patent for the technique.
According to the patent filing, “the method monitors a number of times each content title of a plurality of content titles are downloaded in the peer-to-peer environment, adds one or more content titles of the plurality of content titles that are downloaded above a predetermined threshold to a list, downloads each one of the one or more content titles in the list via the peer-to-peer environment and verifies that each one of the one or more content titles that are downloaded matches at least one content title in the list.”
Or, to put it more simply: AT&T's patent is for crawling search engines and RSS feeds for torrent titles, putting the torrents into a database, and matching that against individuals who are downloading the torrent. The process is shown below.
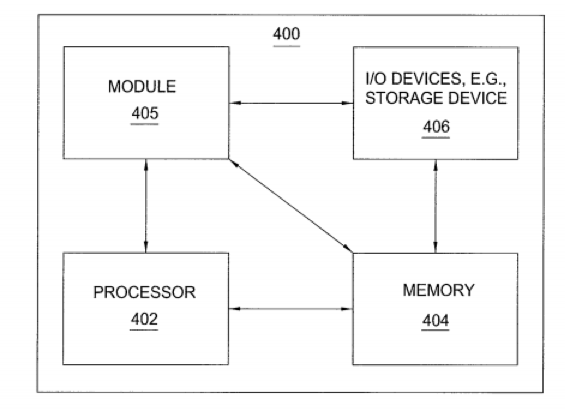
To gain as broad a coverage for its methods as possible, the patent notes that its approach could be implemented in ASICs, general purpose computers or “any other hardware equivalents” - complete with the wonderfully-detailed hardware block diagram pictured.
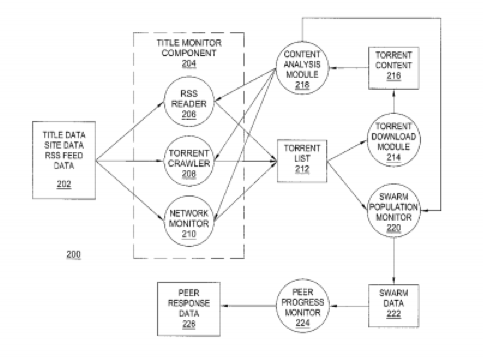
Catch your torrenter: AT&T's patent process
An embodiment of the system: bet nobody thought of that before
One of the issues that plagues torrent analysis is spam files (files misleadingly labelled as a popular title), and virus files posted under real titles. AT&T believes the content analysis capability described in the patent will deal with this.
TorrentFreak notes that AT&T is a participant in a six-strikes copyright alert program in the US. ®
