This article is more than 1 year old
El Reg casts a weather eye over Bureau of Met's new baby
'Meteye' upgrade is a weather geek's dream ... on the desktop
Australia's Bureau of Meteorology runs one of the nation's most popular web sites, and is about to introduce a big new upgrade called 'Meteye'.
It's in beta, and Vulture South, on a slow news day, decided to give it a spin both on the MacBook Pro and on a Samsung Galaxy smartphone.
The short verdict is easy and nearly immediate. If you have a screen and a pointing device, Meteye is no worse than the more traditional BOM site for a quick lookup of the weather; but on a mobile phone, it's a horror.
Let's start on the MacBook. The landing page for the site looks like this:
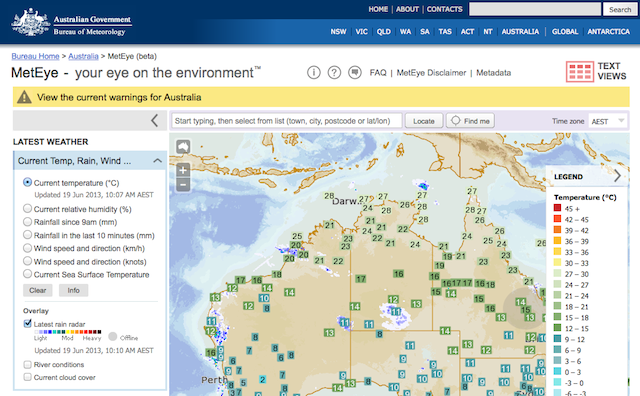
It's a little cluttered, but we can live with that. Since the vultures land in North Sydney, that's the location we skipped to next.
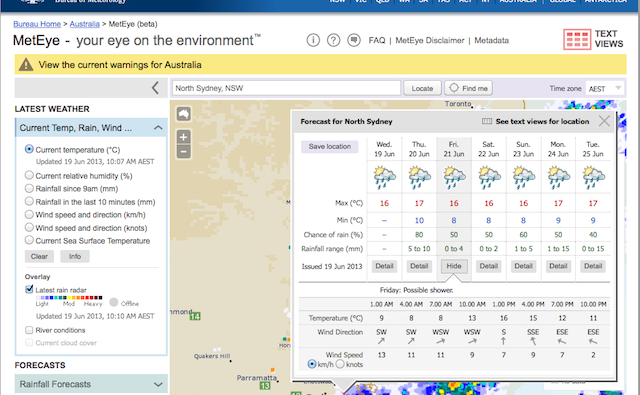
Fair enough. A seven-day forecast, the latest rain radar underneath: all very unexceptional, and straightforward, which is as it should be. There's only one or two oddities – this is after all a beta – such as giving a location a 25 percent chance of any rain when it's currently under a rain cell.
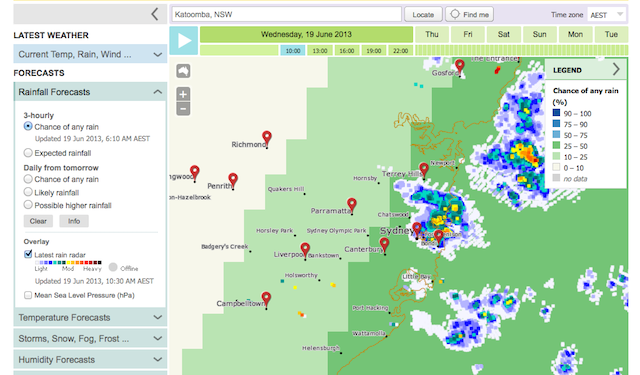
You also learn quickly that you don't need location search: any click, anywhere, pops up the details for anyplace that has a forecast.
But getting the same info out of my mobile phone proved a little more challenging. The problem is simple: too much of the screen is “active” (which makes it hard to drag around or zoom). Touch the screen to zoom it, and the map relocates or opens a popup.
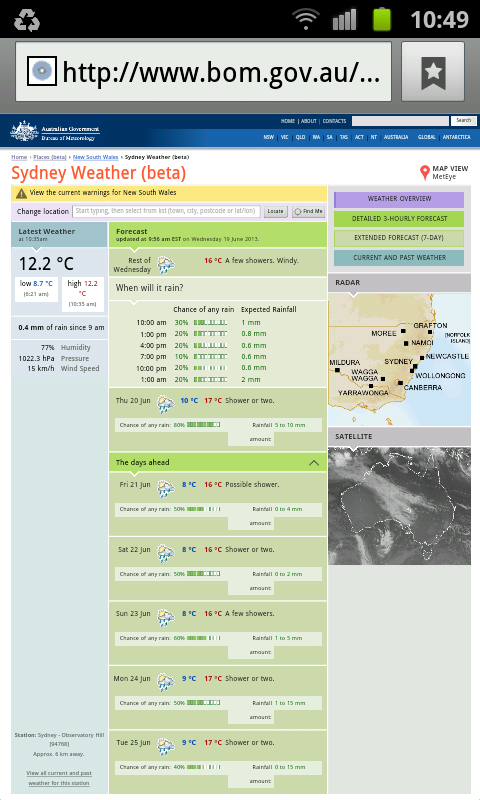
When you do manage to navigate to a forecast it looks okay:
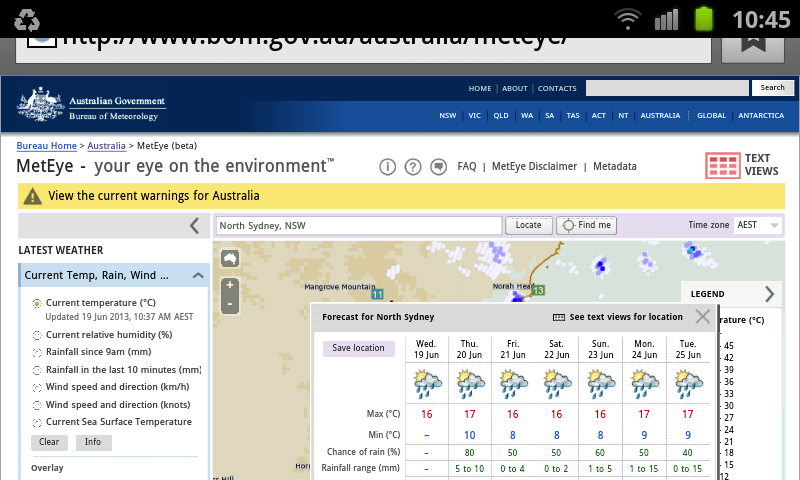
But navigability was so poor that I eventually gave up and headed, instead, to the text version.
At a guess, I'd say the design is much more oriented to tablets than either static machines or mobile phones, but that's just my opinion.
Thank heavens it's only a beta* – and that the BOMers are looking for feedback. ®
* Our link to the beta site stopped working publication. And the Meteye area of the BOM website is password protected.
