This article is more than 1 year old
Boffins build headless robo-kitties
Soft kitty, warm kitty, cuddly little ball of wire kitty
Video Swiss scientists have built a trotting robotic house cat, and say that the form factor could prove very useful for small and agile search-and-rescue robots.
Keep it away from your mouse – though it can't bite
Cats – big and small – hold a particular fascination for robotics engineers (and for much of the internet, it seems), with the animals showing unrivaled speed and agility. There are currently at least two efforts underway to build a robotic cheetah for military use, but the Swiss decided to scale that model down to the domestic cat size, and have seen surprising benefits in thinking small.
"This morphology gives the robot the mechanical properties from which cats benefit, that's to say a marked running ability and elasticity in the right spots, to ensure stability," explains Alexander Sprowitz, team scientist. "The robot is thus naturally more autonomous."
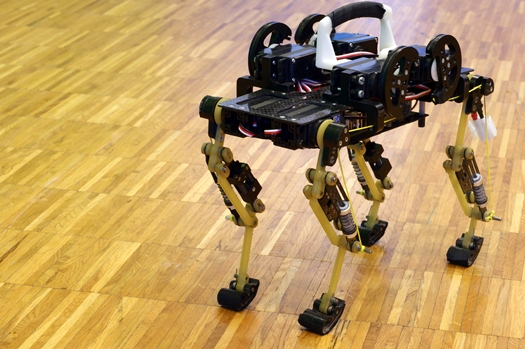
The 1.1kg (2.4lb) device built at the Swiss Federal Institute of Technology in Lausanne stands on triple-segmented 15cm legs and is capable of speeds of 5.1kmh (3.2mph). Mimicking a cat's gait gives the robot stability, and the basic prototype is capable of climbing over obstacles 20 per cent of its height.
The design uses springs and actuators to replace the tendons and muscles of the furry quadrupeds that rule so many a household. The whole system uses between eight and 14 volts to operate.
The end goal is to create a fast, agile, ground-hugging robot that can search out large areas like a cat and with the morphology of a cat, but one that won't get distracted by a light source, butterfly, or its own genitalia like its biological equivalent.
The Swiss machine does require tethering for power at the moment, but its small size makes its requirements much less than its larger military brethren, and thus more easy to power by battery. A "head" of sensors could also be added, helping reduce the creep factor of seeing the thing cantering towards you. ®
