This article is more than 1 year old
Big browser builders scramble to fix cross-platform zero-day flaw
Mac users, you're just as vulnerable to phishing scheme
Browser manufacturers will release an update in the next few weeks to block a new type of malware that exploits a cross-platform flaw that allows attackers access to Mac, PC, mobile, and even games console internet users.
"PC, Android, Mac – the vulnerability hits them all the same," said Sveta Miladinov, founder of the British-based security research firm MRG Effitas, at a Kaspersky Lab meeting in San Francisco on Thursday. "It is being exploited in the wild, but not at a high rate at the moment. I can't say any more until the patches are finished, but it's a true cross-platform browser vulnerability."
Miladinov's team had seen the sample working against one particular browser type and has taken a sample in the wild. By reverse-engineering it, the team showed that the code can be used to get around the security of most of the major browsers. His company then got in contact with manufacturers to get the flaw fixed before going public with the news.
This is the kind of exploit browser makers loath and security experts have come to fear, and it appears that the malware is primarily intended for use in phishing attacks rather than giving access to full systems. More details will be made available once the zero-day flaw patch is released, but even that may not be enough to provide protection.
"For many users, even old attacks are zero-day for them personally, because too few people actually update their systems, especially Mac users," Peter Stelzhammer, cofounder of security researchers AV-Comparitives told The Register.
"It's very difficult to get malware to take control of a fully patched Mac computer, but what's the point? The main problem is phishing and that's browser-based," Stelzhammer said. "It doesn't really matter if it's a PC, Mac, or games console; you're still vulnerable to browser attack."
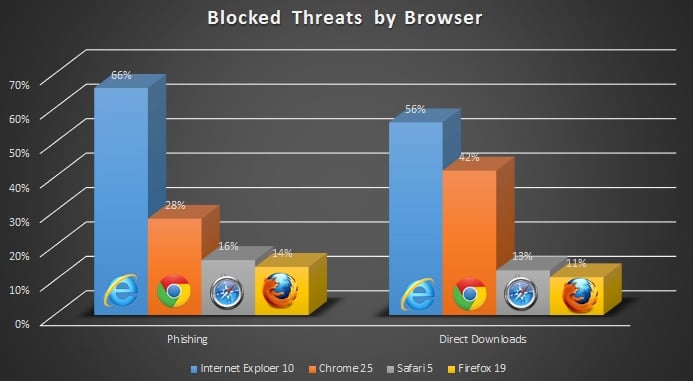
He pointed to recent research from his company that showed that while Safari isn't the most vulnerable browser out there, it's far from the best either. The AV-Comparitives test found that for phishing attacks, Safari stopped just 16 per cent of test malware, slightly ahead of Firefox but well behind Chrome and Internet Explorer.
The going price for a really extensive zero-day for operating systems could be as high as $200,000 on the vulnerability market, according to Tiffany Rad, analyst at Kaspersky Lab's global research & analysis team, and browser cracks are also valuable. But malware writers looking to economize are taking a cheaper option to crack systems.
"If you're a writer, it's a lot easier and cheaper to pack in a few hundred not-quite zero-day flaws into a piece of attack code, throw it out there, and see what sticks to systems," she told El Reg. "Given the updating habits of too many many security-software users, something usually gets through." ®