This article is more than 1 year old
TSA: Perv scanners now fully banished from US airports
New machines spot targets, not todgers
The US Transportation Security Administration (TSA) says it has completed the process of removing all security scanners capable of creating detailed images of passengers' bodies from US airports.
By Congressional mandate, all scanners using so-called advanced imaging technology (AIT), which rendered fliers' nude bodies in Pixar-like detail, were to be either removed or retrofitted with software capable of performing automated target recognition (ATR).
With ATR, the scanner displays only a vague outline of a passenger's body, with generic yellow boxes superimposed to alert security screeners to possible concealed objects.
"As of May 16, 2013, all AIT units deployed by TSA are equipped with ATR capability," TSA administrator John Pistole wrote in a letter to Congress that was made public on Thursday, indicating that TSA actually beat its Congressionally ordered May 31 deadline by two weeks.
According to political news site The Hill, lawmakers on the House Homeland Security Committee were pleased with TSA's timely handling of the matter.
"Because of this action and congressional oversight, TSA will never again use machines to screen passengers that do not obscure their images while maintaining security," said Rep. Bennie Thompson (D-MS).
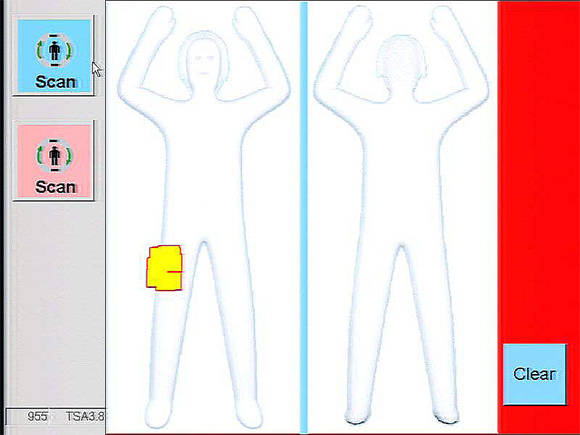
Scanners with automated target recognition might be less precise, but they're certainly more flattering
At issue were scanners based on backscatter X-ray technology, one of two types that TSA had previously deployed. TSA announced that it would stop buying such devices and would begin removing them from airports in January, after manufacturer Rapiscan admitted that it would be unable to retrofit them with ATR software by Congress's deadline.
Body scanners based on the competing millimeter wave technology were all retrofitted with ATR software in 2011 and will continue to be used. ®
