This article is more than 1 year old
INSIDE GCHQ: Welcome to Cheltenham's cottage industry
'If this nerve centre didn't exist, neither would I' says Reg man
Tinker, tailor...
Oakley had its own bar too, and no doubt the thinking behind this was to keep lubricated chatter within the secure confines of the grounds. The fact that the place sold godawful keg bitter – I think it was Whitbread Tankard or Ind Coope Double Diamond – meant that most self-respecting drinkers ended up at The Bayshill Inn. Not exactly local to Oakley but known for a decent pint of Wadworth’s 6X. There was even a mural of regulars painted in there which included an ale fancier from GCHQ. No, you don't have to wear a burqa or similar to work there.
At one point I found myself at The Bayshill Oakley on a training course. During the lunch break I asked a security chap if I could go up the hill to visit my Dad. “Oh no son,” he scoffed, “you’ve not got clearance to go up there.” Needless to say, bring-your-kids-to-work week has always a bit of a damp squib for a lot of families in ’Nam.
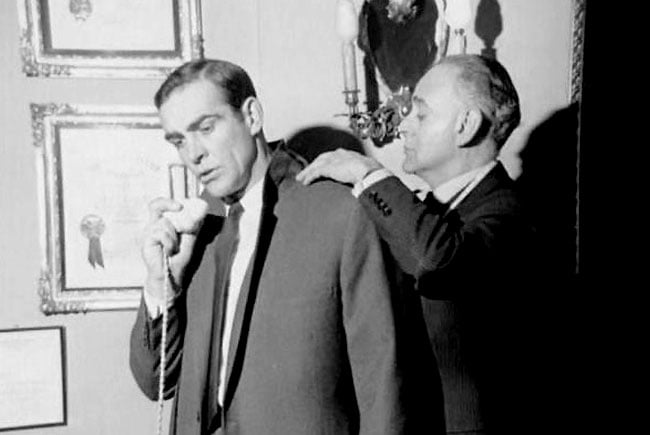
Bond calls for help to decipher the mumblings of his tailor
Source: Anthony Sinclair
Indeed, “how was your day?” tends to be a conversation killer for GCHQ employees too, but I do recall my Dad telling me about a course he attended that sounded a lot more fun than anything I’d been on. The gist of it was to do with context and how information could appear abstract when it lacked any reference points. The way this was demonstrated on the course was to play a muffled recording that sounded like people talking in the adjacent room. The group was asked if they could tell what was being discussed and none could. Then they were told that it was a conversation between a man and his tailor. The recording was played again and, armed with this reference, they could all understand it. I never found out if the mention of whether sir dresses to the left or to the right implied any political leanings.
Just for the record, it’s worth mentioning that the good folk of GCHQ are not of a hive mind and don’t all share the same political views. So don’t think for a minute that snoopers’ charters proposed by the government of the day are universally supported. While the technology may exist to follow a political whim, I’m sure most GCHQ bods would rather be tracking greater dangers than getting bored to death trawling through domestic emails or following misguided tweets.

Source: Dink Cartoons
Talking of politics, Thatcher initially proposed banning unions at GCHQ following the Civil Service strike in 1981, which some GCHQ personnel observed. I remember a handful of pickets at the site entrance, but it was all pretty passive. Still, Mrs T’s thinking behind the ban was that this security service could not be compromised by strike action. There was quite a fuss, to put it mildly.

Badge of honour?
Source: UnionNews
Somewhat naïvely, I was surprised by this as I had tried to join the union myself way before the ban arose. Despite phoning up the local union rep, I didn’t get the followup information I was expecting. The combination of my low wage (I wasn’t exactly looking forward to paying the dues) and the mutual apathy that ensued meant I didn’t become part of the union and was left with the distinct impression that there was no obvious urgency for members.
It’s a pity this didn’t work out though, as Thatcher bribed compensated each GCHQ union member with a £1,000 cash payout for abandoning their respective trade union. The ban finally took effect in 1984 and 14 workers were sacked for refusing to relinquish union membership. It took until 1997 for unions to be permitted once more at the establishment.
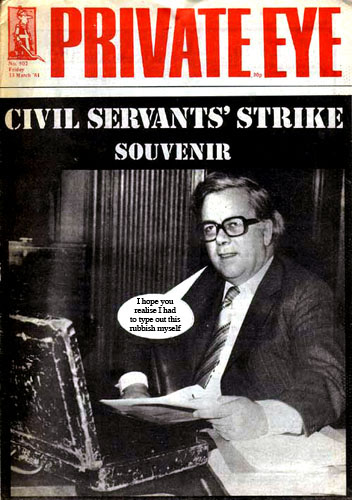
Reproduced by kind permission of PRIVATE EYE magazine
Click for a larger image
I was there when the Falklands War broke out and although the conflict was fairly short-lived, the mood definitely changed during this period. Nobody was being jingoistic, and a single-minded seriousness prevailed. If anything, there was a sense of disappointment that we found ourselves in this situation, as part of the purpose of the organisation was to be so well-informed as a nation that conflicts could be avoided. Remember, GCHQ was there to monitor signals from around the world, as well as what was happening in Blighty.
Another pearl of wisdom from my Dad on this matter was that the Americans had warned us that the Argentines were gearing up for battle way ahead of their invasion of the Falkland Islands back in 1982 and that for some reason, the powers that be here in Britain had ignored this intelligence from our colonial cousins. I’ve no cause to doubt what I was told back then. History is littered with similar situations of intelligence being deliberately ignored or even sexed-up for political reasons.
Anyone who has taken an interest in the tales of secrecy at Bletchley Park during wartime will be aware that there is a "need to know" mindset, where people worked in separate teams without meeting or discussing their tasks with others. When I first heard this phrase at GCHQ I mistakenly thought it meant that one needs to know – like we were sharing stuff in some motivational way.
Of course, the emphasis is actually, do you need to know? Oh well, I was not long out of school so such subtleties were initially lost on me. If people were coming and going in secret, it naturally wasn’t obvious at all. I do recall the "cell" though, which I noticed one or two people emerging from occasionally. It was some kind of high-security broom cupboard, although it could have been like a Tardis inside, but I never found out. I guess I didn’t need to know. Still, it’s no surprise that places like that existed, whether for storing sensitive documents or working in a shielded environment. Maybe there was a Lamson tube in there going all the way to Cheltenham race course bookmakers.
The BBC managed to get a tour of Oakley before the demolition began and produced a couple of videos that include the high-security vaults, massive code-crunching computing areas and a backup power generator that could run the whole town.
