This article is more than 1 year old
BlackBerry Messenger unleashed: Look out Twitter and Facebook
Ignorant tech pundits just aren't down with the kids
Analysis BlackBerry announced this week that its flagship messenger service, BBM, will no longer be tied to its proprietary handsets, potentially opening up a lucrative licensing stream which could rescue the beleaguered mobe-maker.
Fan forums have been in meltdown after the announcement. From some, the pain appears to be personal. Odd as it may seem, I'm not surprised. For teens, BBM is the secret social network that grown-ups don't know about. It does things other social networks can't. No wonder people get attached to it: they feel it's part of their identity.
But even though BBM has millions of enterprise users - particularly in the public sector - for many more it's a complete mystery. Amongst the confused and ignorant are industry pundits and Excel-jockey analysts, very few of whom have ever seen BBM in action. And you very much need to see it live, in a social context, to understand what its real value is. Partly this ignorance is down to class and race.
Avid BBM users are either in far-away countries (Indonesia, the Phillippines) or in what advertisers call the "C2DE" classes - so the white-collar analysts never see them. In fact, they'll make great efforts to ensure their children don't mix with BBM-using children. Literally, they don't know what they don't know.
Yet for my money, BlackBerry's decision is one of the most interesting and potentially far-reaching decisions by anyone in the IT or telco sector this year, so it's worth a detailed look. However, given that BBM is a stranger to many of you, I'll focus on what BBM means for you, and how it could shake up the market.
Capitalising on the unique
BlackBerry Messenger is far more sophisticated than most of the over-the-top (OTT) messaging rivals which have eaten into its market share, and some aspects are pretty unique. One dimension is its reliability, with guaranteed delivery and read receipts. Another, rather better known, is its security - it's odd that the two characteristics are typically munged into one, as 'secure messaging'.
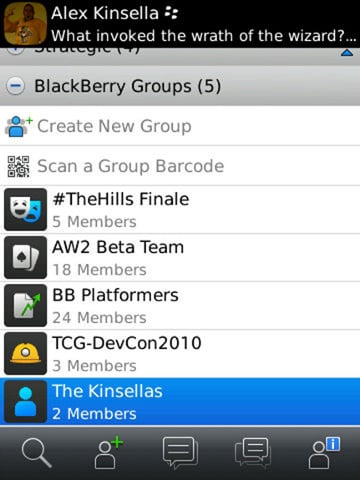
BBM also has rich features, such as the ad hoc creation of groups, as well as groups managed by an administrator, such as “Sales Team”. Some, but far from all, of its rivals also possess groups. BBM also has a variety of ways of connecting, via PIN or QR code. It's also a “platform”, open to third party developers since 2010.
By contrast, rivals offer messaging and (sometimes) voice calls over IP, but these are of varying quality, to say the least. Apple has first rate engineers and a powerful cloud infrastructure, but its iMessage is notoriously flaky. And support for user-created groups is patchy.
The web-based social networks - which really means Facebook Chat and Twitter - have grown flabby and complacent as they've grown. My colleague Bill Ray notes that China's three home-grown Twitter rivals allow ad hoc group creation - but Twitter itself still doesn't. BBM could genuinely shake things up. On top of the basic chat, BBM now offers voice calls, and even screen sharing.
And there's another asset that's overlooked. Since BBM is primarily a mobile social network, it offers context metadata. A BBM user is not only far more likely to present accurate status information but the network knows where they are. Even a little of this - such as whether you're at the office or at home - goes a long way. Facebook and Twitter have no idea, of course, unless you tell them.
