This article is more than 1 year old
The Reg puts Vulture inside the Large Hadron Collider
No sign of any superpowers yet ...
Alarms, airlocks and machines that go 'ping'
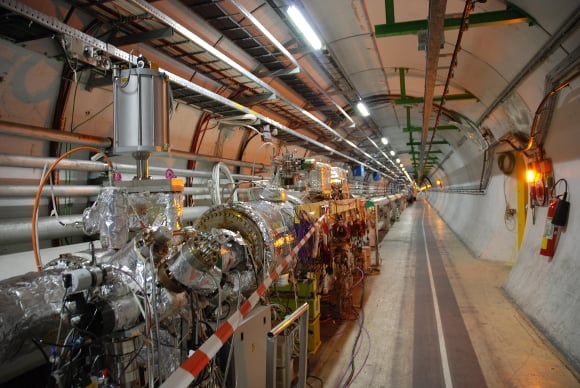
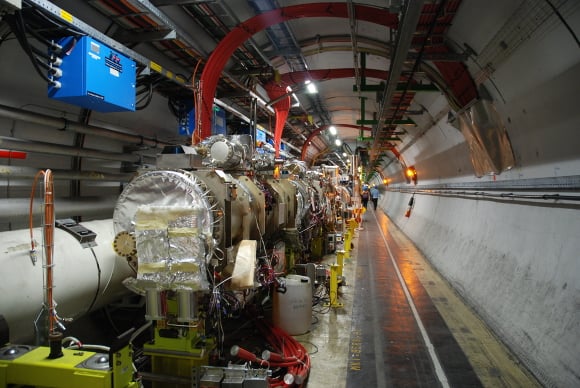
Once through to the other side of the airlock, a very long elevator ride took the group into the tunnel where particles are beamed into LHCb as well as the many other experiments at CERN. Luckily, no one was claustrophobic or intimidated by the tonnes of earth over their heads, or if they were they kept the panic to a minimum as the group got their first glimpse of the tunnel.

Now the place is starting to look a lot more like Black Mesa from Half Life
Work has already started all around the collider to get things ready for when the particles start whizzing around again in 2018. Some of the metal tube the beams pass through has been deconstructed and is held together by that wonder substance, tinfoil.
The particle tube deconstructed
Inside the tube, the particle beams race around in separate pipes in an ultrahigh vacuum, and are then merged for the experiments' collisions. They're guided around the ring by a strong magnetic field, supplied by superconducting electromagnets that are supercooled to -271.3°C - cooler than outerspace - by liquid helium.
Thousands of magnets are at work throughout the LHC, including 15m long dipole magnets to bend the beams and 392 quadrupole magnets, around 6m long, to focus the beams. Don't get too distracted by the incredible science and engineering going on though, you might get left behind by the group...
Wait, where did everyone go?
