This article is more than 1 year old
The Reg puts Vulture inside the Large Hadron Collider
No sign of any superpowers yet ...
The Compact Muon Solenoid
LHC spokespeople are fond of saying that the data produced by the LHC is roughly enough to fill 100,000 DVDs every year, around 15 million gigabytes of data annually, and while a huge amount of that information isn't held by CERN, a considerable amount of computing power is needed to sift through it. Just one long room of that onsite computational heft is an impressive sight. It's arguably the world's most extensive computer system.
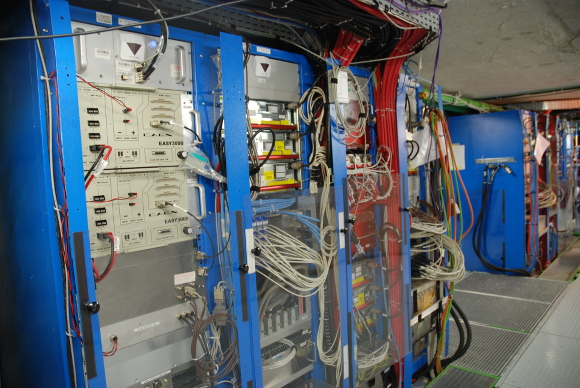
The experiment's computer room, complete with cable nest
But the boffins have saved one of the most impressive sights for last. Leaving LHCb, the group enters the Compact Muon Solenoid (CMS), one of the experiments responsible for spotting the Higgs boson. Outside the apparatus itself, we get to see that we've come a looooong way down. (Any blurriness in this pic is of course down to some sort of camera thing, and not the trembling hands of your Reg hack).

It's a long, long drop to the Compact Muon Solenoid
One of the guides compares walking inside CMS to walking into a particularly stunning cathedral, with the same sense of awe for the accomplishments of man. As much as a cynical and embittered hack would like to be able to disagree, the description is actually pretty accurate. The immense apparatus, full of tiny moving pieces that thousands of people have managed to engineer in a move towards explaining the known universe, is more than a little awe-inspiring.
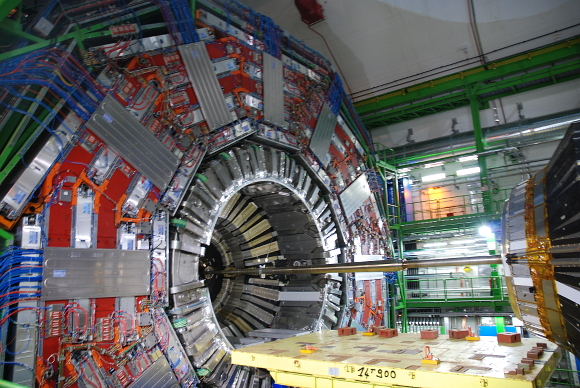
Stepping inside the muon experiment
The only thing that dimmed this Vulture's spirits just a little was that your humble explorer had not started to glow, shrunk to tiny size or developed any super-strength as a result of the close encounter with the collider. ®
