This article is more than 1 year old
Reg readers reveal MIGHTY DOMESTIC DATA CENTRES
Servers’n’sofas challenge reveals racks and stacks in the oddest places
Not a lab but noteworthy anyway
The servers’n’sofas challenge also scared up few entries that aren’t labs, but deserve a mention.
John Robson’s rig, which he used to do some serious work on Seti@Home, represents the most unusual location, as is visible below.

John Robson's alien-finding home lab
The rig is defunct but once comprised 17 PCs “from a P166 (on firewall duties) to a Dual CPU P III 800 (the 1GHz Athlon (water cooled@1.2GHz) downstairs, all on a 10MB hub (not switch) and running flat out doing SETI@Home processing, with a local data cache of three days.”
John notes: “17 PCs in a one bedroom flat was a little excessive, and it has mostly been donated/mothballed.”
We’re happy about that, as the roof cavity location of John’s lab looks a far from ideal location for a computer of any sort, never mind 17 humming away producing heat.
John worried about that too, telling us “the tallest machine (on the left) used to run a little warm - the case still has rubber embedded into the top from when the feet of the keyboard melted.”
David Given had the most exotic rig, as the server he has set up to drive his website and do what he calls “the usual routing/caching/proxying/firewalling/fileserving roles” has a motherboard built from “a customised Mele A1000 set-top box, based on a Cortex-A8 ARM core with 512MB RAM. For storage it has a 64GB Kingston SSD and 2TB Seagate spinning disk.
“The big black square on top which makes it hard to photograph is a sound-absorbing baffle made out of a neoprene mouse pad. The console is an old laptop plugged in via USB.”
Ashley Black runs a mail server VPN he uses to access resources at work and a home network from “the little under-stairs cupboard that even Harry Potter would find cramped.”
J.J. Green sent a shot of a defunct under-the-stairs lab that included a stuffed soft toy penguin, which seems fitting and earns him a mention.
Lastly, let’s all bask in the diagrammatic glory of Tim Stone’s effort.
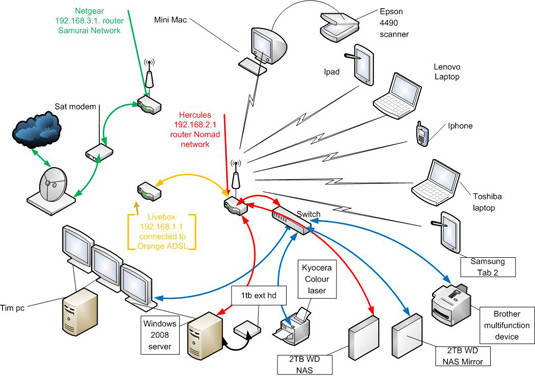
All this to trade shares
Tim was the only one to send us a network diagram. It depicts a rig he uses for day trading.
The Reg wishes Tim and all those who took time to send us descriptions and images of their home labs all the best with their efforts. And their power bills. ®
