This article is more than 1 year old
Micro-drum acts as quantum memory
NIST puts qubits in a spin
Memory is one of the difficult bits of quantum computing. For example, while the polarisation of a photon encodes a quantum state, it's very difficult to get photons to stay where they're put.
A group of researchers from JILA – a joint institute between the University of Colorado and the National Institute of Standards and Technology – has demonstrated a different approach to capturing quantum states in memory: they're using a microscopic spinning platter to do the job.
At the moment, it's not very accurate: the spinning drum captured the vertical and horizontal positions of a microwave signal at a point in time (the quantum state they were trying to capture), but that state could only be retrieved with 65 percent accuracy.
The micro-drum was created by NIST in 2011. Because it's embedded in a resonant circuit, the drum is able to beat at different frequencies. That means the electrical energy in the microwaves can be captured as mechanical energy as a phonon (a unit of vibration).
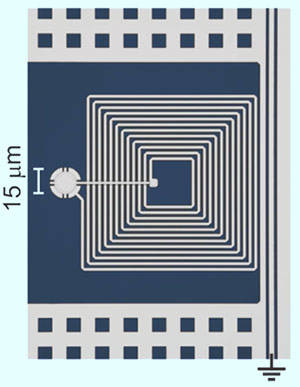
NIST's micro-drum and circuit (colorised image)
To get this interaction happening at the quantum level, the researchers had to cool the drum to its lowest-possible energy state, at which point it has less than one quantum of its own energy. The microwaves used to cool the drum to its ground state also transfer information about the their quantum states to the drum, in the form of a temporary state beating at the received frequency.
The researchers also found a way to turn the microwave-drum interaction on and off, based on the intensity of the microwave tone.
If the researchers can improve the performance of the quantum memory, they'll end up with something that's compatible – both in size and in the fabrication techniques used – with devices that NIST uses as qubits.
NIST says in practice, the micro-drum is somewhat like the delay-line memory used in early computers like NIST's SEAC of the 1950s, in which computation values were temporarily stored as acoustic waves travelling down a column of a fluid like mercury.
The NIST research is to published in Nature and its announcement is here. ®
Bootnote: The researchers note that the drum is actually a quasi-quantum memory: its beat is a classical system, but in a quantum-noisy environment. This author isn't physicist enough to completely understand the distinction. ®
