This article is more than 1 year old
Happy birthday, LP: Can you believe it's only 65?
From scratchy spinner to flash and now the cloud
This storage medium progressed from spinning disk to flash and then entered the cloud... Sound familiar? It's the long-playing music album and this year marks the sixty-fifth anniversary of its inception.
The 33 1/3rpm vinyl long-playing record was devised in 1948 by Columbia Records and was an upgrade on the prior 78rpm 12-inch shellac records - which were noisy, read by a needle tracing the surface of a spiral grooved track, and only played music for about five minutes.

Some 78rpm records
Like the '78', the 10- or 12-inch long player (LP) used analog recording and was two-sided but the 'microgrooves' were finer, so the track was longer, and the playing time was 20 minutes or more.
Then stereophonic sound was added and the album became the standard way of buying classical music, collections of pop singles and then popular music and songs created as an entity rather than as a set of three-minute singles. There was glorious album art and breath-taking musical adventures but the technology had limitations.
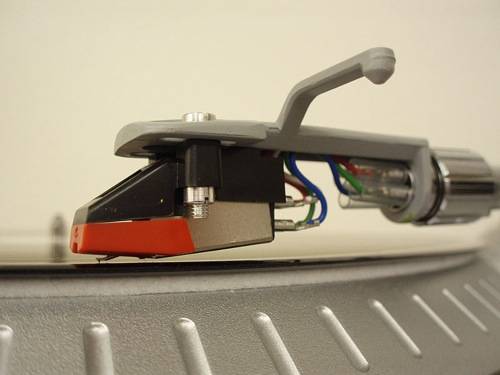
LP record stylus
Records wore out because the needle scratched the microgroove surface and so music and song quality suffered. The LP had to be turned over after 20 minutes to play the second side. The player with stereo amplifier and speakers was not portable. Playing individual songs was a hit-and-miss affair as you had to locate them on the LP's surface.
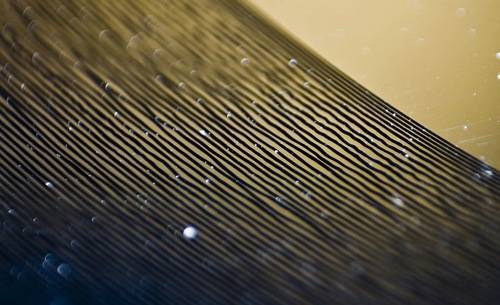
Vinyl record grooves

In the early '80s, Sony's Walkman became the first popular answer to the portability problem - a small battery-powered tape cassette player with headphones. This was good as far as it went, which was not far enough because the CD - which started catching on towards the end of the '80s - swept the cassette-based Walkman away.
In the the late 1980s, music fans were blown away by the new high-fidelity recording medium. The compact disc is an optical technology, so while the single-sided discs still had spiral tracks, the signals pressed into them were read by laser. Unlike the old LP, there was no contact with the disc's recording surface, which was covered by a transparent layer of plastic. That didn't stop them from getting scratched though.
