63
This article is more than 1 year old
Thunderbolt interface strikes YOUR PC: What's the damage?
10Gbps, you say? Now for the reality check
Benchmark Tests
AS SSD Sequential Read
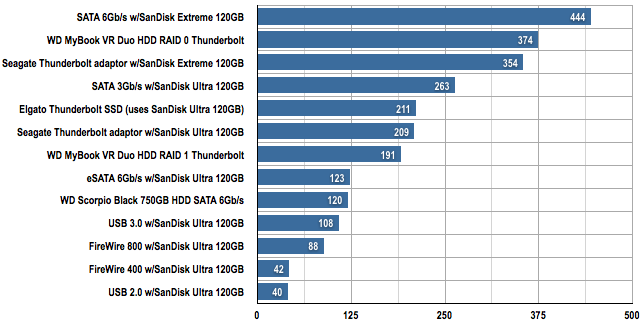
Data transfer in MB/s (longer bars are better)
AS SSD Sequential Write
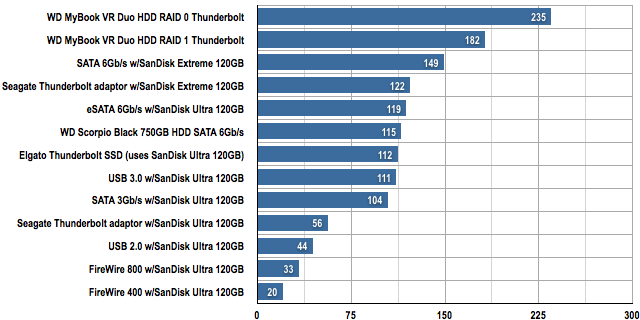
Data transfer in MB/s (longer bars are better)
4GB Image Copy
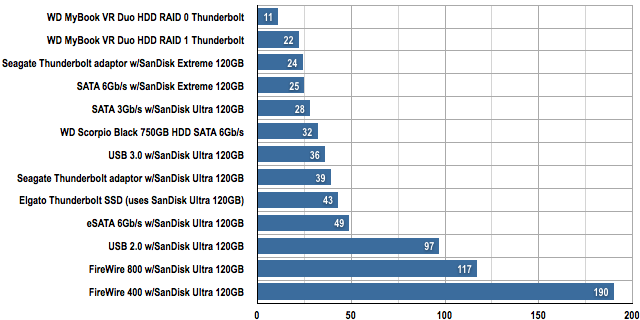
Copying time in seconds (shorter bars are better)
50GB Mixed Files and Sizes Copy
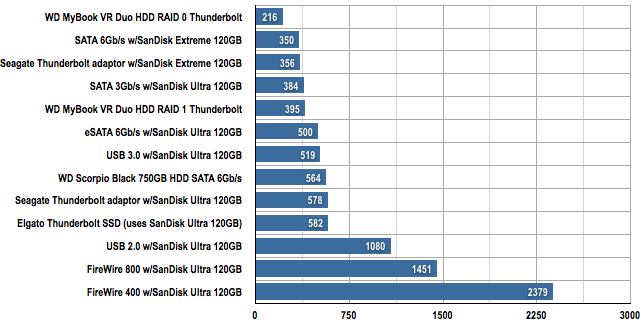
Copying time in seconds (shorter bars are better)
17GB Blu-ray File Copy
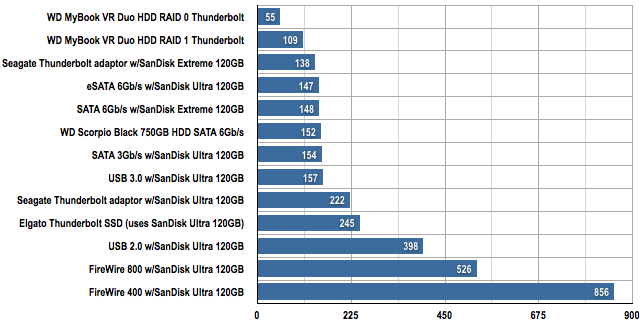
Copying time in seconds (shorter bars are better)
