39
This article is more than 1 year old
Steve Bong's 3D printing special Xmas showcase
Join the MAKERS' REVOLUTION with these INCREDIBLE GIFTS

Today it's just a child's safety bike - tomorrow, you'll be able to print out your own personal transporter in seconds using 3D printing. Cancel that taxi!

This stunning replica of the powerful Delta IV rocket hints at the potential of 3D printing. Advances in additive manufacturing mean this could soon be launching from a back garden near you.
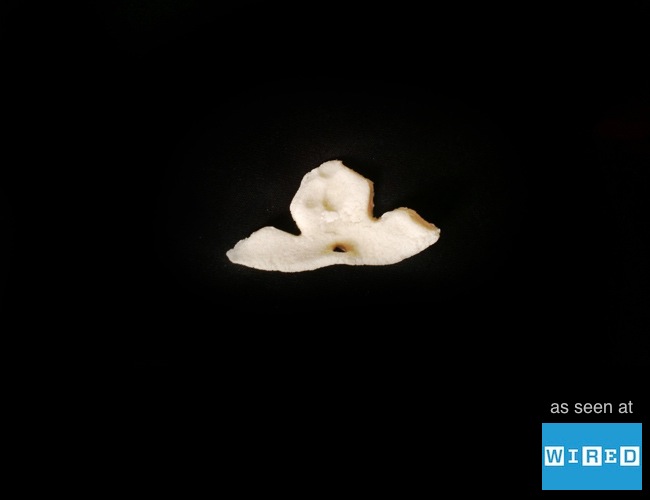
It may look a humble wingnut, but this is actually a vital component in a Tokamak nuclear fusion reactor. Decentralised power generation can become a reality, and fuel bills a thing of the past, all thanks to the imminent manufacturing revolution of 3D printing.
Power to the People!
®
