This article is more than 1 year old
The 30-year-old prank that became the first computer virus
Elk Cloner creator Rich Skrenta looks back
Collaring the culprit
Friends may have cursed Skrenta and then, seeing the joke, chuckled at his antics, but not everyone was impressed by the humour or the programming skill he demonstrated. The first person to confront Skrenta about his antics was one of his teachers.
“The maths tutor confronted me as I was taking off my coat. He accused me of going into his office and hacking his computer,” Skrenta says. To this day, he doesn’t know how the teacher concluded he was the prime suspect, figuring it was his clear enthusiasm for computers that gave the game away.
But, aside from the maths man, there was was “no major reaction” to Elk Cloner, something Skrenta viewed as a “silent victory”.
Rich Skrenta in 1989
Source: Northwestern University
“The virus is fairly harmless, had no network connectivity, and problems were solved by a reboot,” he says.
Skrenta created a utility to remove Elk Cloner from infected discs, again written in assembly language. He never thought of making his applications widely available. There was certainly no need for a more sophisticated Apple II malware scrubber since neither Skrenta nor anyone else created a virus for the platform.
He’d had his fun. “Elk Cloner was it for me and the virus world,” Skrenta explains.
Skrenta went on to study computer science at university where he had access to a mainframe that had more memory and was obviously much faster than the Apple II. This was around the time MS-DOS machines became commonplace.
“I didn't want to own IBM PC and the next computer I had was a minicomputer running a version of Unix,” Skrenta remembers. He's since had some exposure to Windows machines and the computer viruses that often infect them in recent years, much like anyone else.
Early malware for non-PC devices - Elk Cloner on the Apple II, BHP on the Commodore 64 - came five years before Brain, the first Windows PC virus, in 1986.
“PC are always going south with God knows what," Skrenta says. “So I’ve used Macs for the last few years.”
Not that he blithely accepts or trots out the line that Macs are somehow invulnerable to infection. “Macs have switched to a Unix core but there’s always a way in,” he admits. Indeed, the Flashback Trojan that used a Java exploit to infect Mac OS X machines earlier this year demonstrates that today’s virus writers - not jokers like Skrenta was - are targeting the platform.
The start of 30 years of malware
Were they inspired by Skrenta’s work? Skrenta doesn’t think so. "I don't think [Elk Cloner] had any effect on subsequent malware development," he says. “The Brain virus was created by two brothers without any knowledge of Elk Cloner.”
Like Elk Cloner, the Brain virus, written by Pakistani brothers Basit and Amjad Alvi, was relatively harmless but spread widely. This proved to be an exception to the general rule of subsequent malware development.
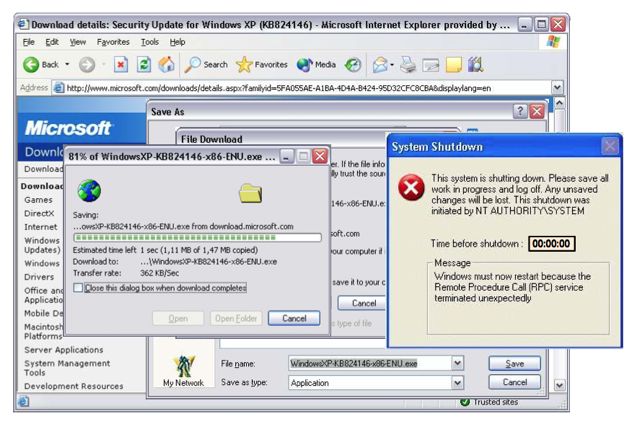
“Early on, all PC malware just infected floppies,” says Mikko Hypponen, CRO at Finnish anti-virus firm F-Secure. “Then we started seeing file infectors, infecting COM programs. They were still spreading between devices as they were carried on floppies.
“Things started changing quickly when the internet came around. First email worms [Anna Kournikova and Love Bug], then internet worms (Blaster, Slammer, Sasser, Code Red etc). And on to malware that's spread via exploits on websites, which is where we are today.”
Money-making with malware started just ten years ago. This brought banking Trojans, often developed with cybercrime toolkits such as ZeuS and SpyEye, and botnet agents to send spam or launch DDoS attacks from compromised hosts, into the picture. More recently, targeted Trojan attacks aimed at cyber-espionage, cyberweapons such as Stuxnet and Android malware have all become a headache.
Three decades after the creation of Elk Cloner, boot sector viruses remain a problem, says Hypponen, but he reckons their days may, at long last, be numbered.
“We've suffered from boot-level malware from the very beginning,” he said. “Elk Cloner, just like Brain and many of the early Apple and Mac viruses infected boot sectors. Arguably one of the most common examples of malware today, ZeroAccess, infects the boot sector of a Windows box.
“In all of these cases, the malware boots up first and then boots up the operating system after it has loaded itself. Hopefully the UEFI boot feature in Windows 8 will finally end this.”
Back in the early 1980s, references to Elk Cloner were few and far between. It wasn’t deemed worth of newspaper reports, for instance. But over the years it has become a bigger story. Skrenta's role in the creation of the virus only came to wider attention after he wrote a letter to Scientific American on the subject, which led to a larger article in March 1985 on the (then not extensive) threat posed by computer malware.
“For the first ten years [Elk Cleaner] was a non event,” Skrenta admits.
Skrenta went on to work in computer security between 1995 to 1998, specifically on a cryptography project with Sun Microsystems, before continuing a successful career in information technology, most recently as the CEO of search engine start-up blekko.
Today, he reckons the industry has got its priorities wrong. “The anti-virus industry makes me sad,” he says. “We should build systems to be more resistant to computer viruses rather than have a multi-million dollar industry to do clean up.
“If more people knew about Elk Cloner at the time perhaps it would have led to more secure OS development.” ®