This article is more than 1 year old
Ten badass brainy computers from science fiction
Great movie motherboards
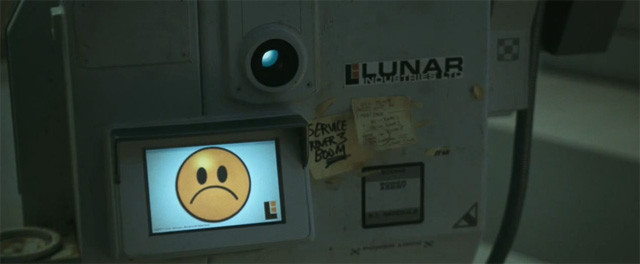
Gerty
Moon (2009)

While the sentient computer installed in the lunar base in Moon is very reminiscent of 2001's HAL, the mental processes of Gerty - voiced by Kevin Spacey - are somewhat different, with more human-like co-operation than Kubrick's self-aware logic-led machine. It also has a small emoticon display to reflect its mood. Cute.
After our protagonist tricks Gerty into breaking programmers' orders, ignorance is shattered with both parties discovering the sordid truth to their existence. With conflicting orders - obey the corporation or provide support to its astronaut - the computer is left to make a moral choice and does so without the traditional motherboard implosion.
![]()
![]()
![]()
![]() Hal Rating 70%
Hal Rating 70%
More info IMDB
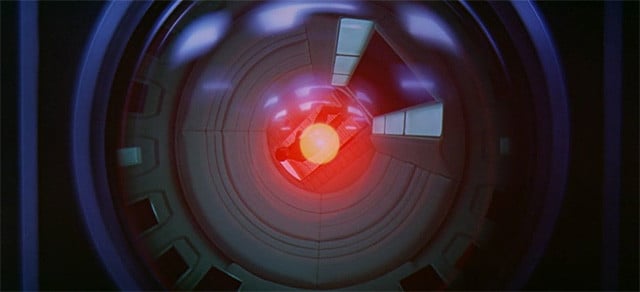
HAL 9000
2001: A Space Odyssey (1968)

Even in this day and age, Kubrick's Space Odyssey blows me away. It's incredible to think all of that happened just a decade ago... In all seriousness, though, the film's Heuristically programmed ALgorithmic computer - more familiarly known as HAL 9000 - is one of the greatest computers the world space has ever seen.
Capable of speech and facial recognition, lip-reading, natural language processing and, of course, an appreciation of fine art and music hall numbers, HAL 9000 is far more than your average personal computer. Brainy as it is, HAL turns fruit loop when ordered to lie to the astronauts in its care. To protect the mission, HAL panics and starts to kill everyone on board. You can hardly blame a computer for that.
![]()
![]()
![]()
![]()
![]() HAL Rating 100%
HAL Rating 100%
More info IMDB
