This article is more than 1 year old
EMC flash man: PCM will save us from the Incredible Shrinking NAND
Someone must've ironed out Phase Change Memory's kinks
EMC's flash exec expects Phase Change Memory - one of the possible non-volatile successors to flash - to appear in storage architectures from next year.
Phase Change Memory exploits the differing resistance levels in chalcogenide materials as they change from an amorphous to a crystalline state and back again, background here.
It is anticipated that, as NAND process geometries shrink beyond 15nm or so, the working life will fall off drastically, speed will slacken and the error checking and correction logic will become much more complicated. At that point, roughly, it is hoped, a post-NAND technology will be productised and deliver chips that are denser than flash, faster than flash, approaching DRAM speed, byte-addressable instead of block-addressable, and with a longer working life. That seems like a real big ask.
Micron, IBM, Hynix and Samsung are are all involved with PCM technology, and Micron recently announced it had started mass production of PCM chips. However they are involved in other post-NAND technology possibilities as well... None of them has committed wholeheartedly to PCM and there have been problems with building chips with sufficient capacity, speed and storage density. Notwithstanding these issues, EMC has voted for PCM.
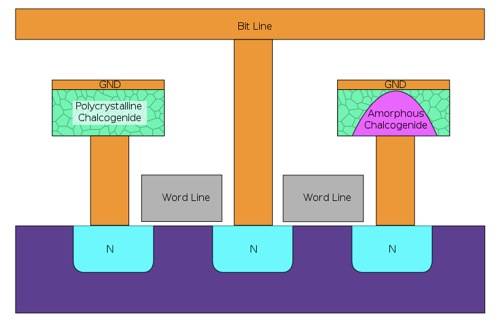
Schematic diagram of PCM cell
Zahid Hussain is EMC's SVP and flash product division general manager, and he has a couple of predictions for 2013. Firstly, he predicts greater use of flash:
In 2013, flash is no longer the future game changer - it's now the norm, ubiquitous in all storage architectures." No surprise there ...
Secondly, he adds:
In 2013, we will see a flurry of investment activity in PCM-based architectures. With this non-volatile random-access memory, the industry will begin to augment existing offerings and deliver an alternative extremely fast storage option with even lower latencies than flash technology, beginning to approach DRAM type of speeds.
EMC is working with Micron on its VFCache PCIe flash cards and its Project Thunder box of VFCache cards. Perhaps Micron is more positive about PCM's prospects in private than in public and has been sending PCM messages EMC's way.
The company seems to be anticipating quite wide PCM adoption: "We will see a flurry of investment activity in PCM-based architectures," Hussain said.
So who else is going to jump? Perhaps Hussain knows something we don't - El Reg's guess is that Micron is deeply involved in telling him what that something is. ®
