This article is more than 1 year old
Ten weird Chinese mobile phones
Star-shaped, quad-SIM and sports car phones
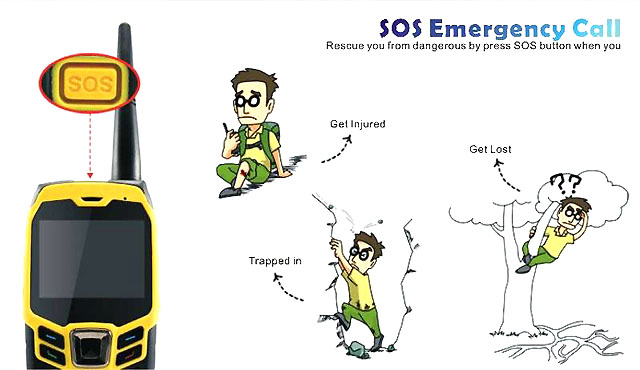
Concox GK3537 rugged walkie-talkie GPS phone

Rugged phones are nothing new. But rugged phones with two SIMs, a built-in walkie-talkie, a torch and an emergency GPS beacon aren't waiting to be plucked off high street shelves.
Happily Concox & New Thinking Group of Shenzhen has all that covered, in case any of the fates illustrated below should befall you.
And it's nice to see external aerials making a welcome return to "sports phone" design.
Price $188 (£118)
More info Concox and Mobile-Phones cn
Concox GPS GK301 Teddy phone

Simple mobiles for kids have occasionally targeted parents worried that little Xavier or Anastasia might get mugged between the school gate and the Land Rover.
This creation, a product of Concox & New Thinking, seems to be aimed at kids who need to phone a friend when they can’t solve a puzzle on Dora the Explorer.
They're bound to do so because, as Concox so eloquently puts it the phone's marketing material, “Colorful design of lovely baby bear appearance attracts kids attentions”. Once so attracted, kids need only mash one of four pre-programmed buttons to make a call. You can also track your kids thanks to the phone’s GPS module.
Concox's fondness for a bit of prose extends to having a destiny, part of which is "To live in peace and work happily; to promote harmonious growth". We do hope this catches on: 'destiny statements' would be a lot more interesting than boring old 'mission statements'.
A lanyard is included with the phone. We’ve no idea if it has been tested to withstand or properly distribute its 58g weight, or if children’s spines will need prophylactic paediatric chiropractics before it can safely be used. To parents considering this phone that undertake that research, feel free to let us know your learnings.

Price $55 (£34)
More info Concox and Protective Electronics
