This article is more than 1 year old
Druva: We can do a mixture of anything you can do
Voodoo that we do quite different from that which you do
Mobile, desktop and notebook backup startup Druva has dropped file sharing into its product mix and reckons it's distanced itself from pure-play endpoint backup vendors and file sync 'n' share players.
Druva was founded in 2008 and says its software is used to protect more than a million endpoints - desktop and notebook PCs, and mobile devices. Druva rekons it competes with Connected, Crashplan, and Mozy, plus - to a small degree - Dropbox and Symantec, in the endpoint protection business.
Now that file sharing has been added to Druva's InSynch v5.1 client device backup product the company competes with Box, Dropbox, Egnyte (story here), and (to a small degree again), Dropbox and Symantec in the enterprise file-sharing business.
Druva's positioning pitch now, according to the chart below, is that it is a better endpoint backup facility than any of its competitors - but not as good at business-grade file sharing as Box and best-in-class Egnyte.
Borge Rosales, Druva EMEA managing director, said that his firm will add:-
- App-integration
- Server folders
- Better collaboration with people outside the enterprise
- Backup settings facility
- Archival and legal hold
- Document tagging
- Document Rights Management
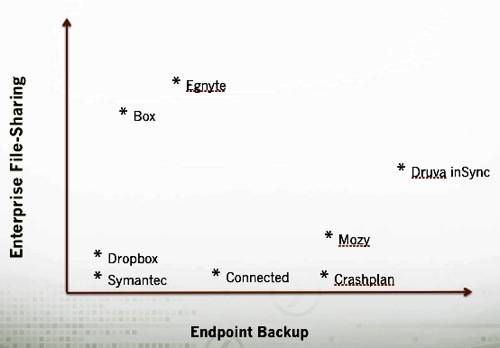
Druva's idea of competitive positioning for InSync
Acronis, another backup vendor, is also moving into file sync 'n' share. We wrote up its plans here.
Backup vendors typically have compression, deduplication and data moving software; and cover endpoint devices to some degree. Moving into file synchronisation for these client device is a natural step to make. ®
