This article is more than 1 year old
The early days of PCs as seen through DEAD TREES
The golden days of computer mags, replete with ancient adverts

Byte, January 1988: Many of Robert
Tinney's Byte covers went on to become
collectors' items. Byte even picked up
a few bucks selling poster versions.
(click to enlarge)
Byte, January 1988: 'DESQview is the
"proven true" multitasking, multi-
windowing environment for you. Best
of all DESQview 2.0 is here now...'
(click to enlarge)
Byte, January 1988: Want 512-by-482,
24-bit color with an 8-bit alpha
channel? In 1988, you'd give AT&T
$4,995 – which would be $11,650 today.
(click to enlarge)
Byte, January 1988: 'Over 500 million
reels of magnetic tape are in use
by most mainframe and minicomputer
systems,' and Flagstaff wants to help
you read 'em. (Great hair, as well.)
(click to enlarge)
Byte, January 1988: 'Oracle
Corporation, the world's fastest-
growing software company, has just
climbed past Ashton-Tate to become
the world's larges supplier of
database management software and
services.' (cf. Virginia Slims, above)
(click to enlarge)
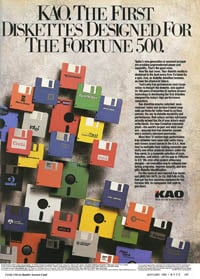
Byte, January 1988: Floppy disks, the
buggy whips of a new generation.
What's next to disappear from the PC
arena? Optical disks? x86 processors?
(click to enlarge)
Geek roots not forgotten
Even as computer magazines of the 1980s broadened their focus to a more general range of consumers who were using their PCs as business tools and home-entertainment fun-providers, they didn't abandon their more-technical audience. Even Mac mags found geeky things to write about.
MacUser January 1986 "Calling All ROMs" by Neil Shapiro: According to some people, writing programs for the Macintosh is similar to wearing a velvet, fashionably-cut straightjacket. No one, least of all yourself, will notice the restraints up until the time to flap your arms wildly about.I once heard a programmer refer to [Apple's UI guidelines] Inside Macintosh as Apple's version of Mein Kampf. He was only half joking.
MacUser also worked to keep its readers informed on the latest inner workings of their favorite computer company – such as one development that would have wide-ranging consequences.
MacUser January 1986 "West Coast Report" by Michael Wesley: It has been a quiet week in the West Coast. Steve Jobs resigned his position as Chairman of the Board of Apple Computer and announced his plans to form a new company to make computers for universities.At the time of this writing, there's no way to predict how the squabble between Mr. Jobs and Apple will be resolved.Whether the dispute will have any immediate or long-term impact on Macintosh is yet another question.
Even developers weren't forgotten in those days' mags – a group to whom consumer-level magazines rarely speak here in the 21st century. In addition to such articles as January 1986's "The Great Language Face-Off", featuring a comparison of BASIC, C, Pascal, and Forth, MacUser published how-to articles for devs.
MacUser January 1986 "Alpha-Beta Soup" by David Levy: David Levy, chess grandmaster and expert on computer games, shows how to program and use an Alpha-Beta search algorithm.
It may be hard for all but the most die-hard networking folks to remember at this point, but there was once an Ethernet competitor that received more than a little ink, such as the following article in PC Magazine.
PC Magazine January 1987 "The IBM Token-Ring Network" by Frank Derfler: The IBM Token-Ring Network is to networks what the Boeing 747 is to airplanes. It makes strange noises and requires special handling but can carry heavy loads. It offers power and flexibility but demands skilled management and control. It is one of the fastest things flying but not one of the prettiest.
Byte, as usual, was more focused on the hard-core computer user, even in its reviews. By 1988, you wouldn't expect to find a comparative roundup up SQL RDBMes in any other mag of the time – or, for that matter, find a review of a decidedly non-consumer device such as a portable Unix box.
Byte January 1988 "SQL Database Management Systems" by Richard Finkelstein and Fabian Pascal: Everybody seems to be talking about SQL (Structured Query Language) for relational database management systems (RDBMSes). But even though most major database suppliers have announced future support of SQL in their products, only a half-dozen database software packages for the IBM PC or XT currently claim to use SQL: Informix-SQL, Ingres for PCs, Oracle, SQLBase, XDB II, and XQL.>Byte January 1988 "The Symmetric 375: Symmetric's new system brings Berkeley Unix to a portable box" by Patrick Wood: The Symmetric 375 computer is a small, portable Berkeley Standard Distribution (BSD) 4.2 Unix system loaded with many useful features. Its small size (about that of Compaq Portable II) and weight (22 pounds) make it the only portable BSD Unix system I know of. The system reviewed here (which includes a bundled terminal and printer) is $8,995, but Symmetric discounts the price to $8,095 if it is prepaid.The Symmetric uses a National Semiconductor NS32016 processor running at 11MHz with no wait states and a 64-bit NS32081 floating-point processor.
Byte also ran more big-think pieces in those far-away days, although I may be speaking through my prejudice, being a devotee of that magazine – as if you couldn't already tell. For example, one 1988 article presages the arrival of an all-things-to-all-users global content access and sharing system: "Project Xanadu, The Original Hypertext Project". Think of it as an alpha-level internet.
Byte January 1988 "Managing Immense Storage" by Theodor H. Nelson: Project Xanadu is a system designed to be the principal publishing utility of the future. It will provide for the deposit, delivery, and continual revision of linked electronic documents, servicing hundreds of millions of simultaneous users with hypertext, graphics, audio, movies, and hypermedia.
Even when writing about such commonplace items as the ubiquitous floppy disk – as other magazines did at the time – Byte's reporting was more thorough than most.
Byte January 1988 "Price of Floppies Doesn't Guarantee Quality, Testers Say", news report: Despite wide variations in the cost and quality of floppy disks, there's no apparent relationship between the two, according to a company that has done a comparative study of 5 1/4-inch floppy disks.
But even though developers and hardware enthusiasts weren't forgotten during this transitionary period, advertisements began to appear that pointed toward a future that, although it included the geekerati, was clearly aimed at a broader market.
PC Magazine January 1987 "Interlude II" advertisement: Interlude II, the long-awaited sequel to the first adult computer game is finally here. It's provocative and playful! Outrageous and romantic!It probes your innermost desires to discern your mood of the moment, your secret longings, your special fantasies, then suggests for your pleasure one of its more than 160 Interludes.Interlude II will take you to the outer limits of fantasy and romance. And if the computer selects Interlude #99, your love life may never again be the same.
With the internet still years in the future, in 1987 soft-core smut was still delivered at the application level.