This article is more than 1 year old
The early days of PCs as seen through DEAD TREES
The golden days of computer mags, replete with ancient adverts

Byte, January 1983: The Heath HERO-1
'microcomputer-controlled robot' shared
a cover with Compaq's loveable luggable
and Epson's QX-10 Valdocs System
(click to enlarge)
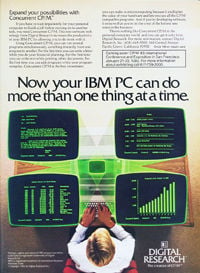
Byte, January 1983: 'Using Concurrent
CP/M, you can run several programs
simultaneously, switching instantly
from one program to another'
(click to enlarge)
Byte, January 1983: In the early days of
personal computing, everyone got into
the act – even Epson, which bought an
eight-page, thick 'n' glossy–stock ad
to flog its QX-10 CP/M-or-DOS PC
(click to enlarge)
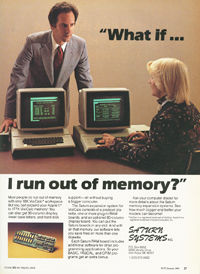
Byte, January 1983: 'Most people do run
out of memory with only 18K VisiCalc
workspace. But you can expand your
Apple II to 177K VisiCalc Memory!'
(click to enlarge)
Byte, January 1983: Tecmar thought
that the low, low price of $1,795
for its 5MB SyQuest–cartridge drive
was something worth shouting about
(click to enlarge)
Byte, January 1983: Thirty-two 150ns
16Kb SRAM chips add up to a capacious
64KB 'state of the art' S-100 board
that costs a mere $629 ($1,470 today)
(click to enlarge)
In Byte, the discussion was deeper – much deeper
While Time was a mass-market glossy that reported on the personal computing phenomenon only after said phenom had bubbled to the surface of the American consciousness, Byte: the small systems journal, on the other hand, was a phenomenon of its own, a deep-geek rag that had been published since September 1975, first appearing only eight months after Popular Electronics' January issue that had introduced the world to the Altair.
Before Time's adulatory PC article appeared, Byte – which focused on machines known in the argot of the day as microcomputers (or, to the French, micro-ordinateurs) – was the must-read rag for the personal computer geekerati. Not only did it carry the latest news of the latest products, it also published – unimaginable now in a broadly-selling publication – page after page of code and circuit diagrams.
And it was larded with advertising. Byte's January 1983 issue – the same month that Time proclaimed the personal computer as The Machine of the Year – was an astonishing 544 pages thick. By comparison, the next time you find yourself at a newsstand that still stocks one of the few remaining computer magazines, pick one up and check out its page count. Sad, isn't it?
Blame back-of-the-book ads, catalogs, the internet, and other factors – but more on that later.
A look at Byte's January 1983 issue – $2.95 in the US, £1.85 in the UK – illuminates how different the world of micro-ordinateurs is, here in the future, than it was in the pioneer past:
Byte, January 1983 "Review: The Compaq Computer" by Mark Dahmke: The Compaq computer is designed to be portable, and although it weighs 28 pounds, it achieves that goal.The Compaq's floppy-disk drives have major advantages, including 320KB of storage capacity each.An IBM PC with one double-sided drive (320K bytes), both the monochrome and color-graphics boards, a parallel-printer port, a monochrome monitor, and 128K bytes of RAM would cost approximately $3,735. All of these features are standard on the Compaq for $2,995.
The Compaq, by the way, was powered by a 16-bit Intel 8088, had a socket ready for the "future addition of Intel 8087 coprocessor," and 128KB of RAM expandable to 256KB. If you wanted to upgrade to a two-floppy system, that would run to $3,590, which in today's dollars would equal about $8,350.
In his editorial in that January 1983 issue, Byte's editor in chief Chris Morgan was ebullient about the personal-computer market that his mag had been following since its infancy. "The industry's new product fever rages on," he wrote, "spurred by record growth in sales and profits."
Morgan also demonstrated his optimism is an article about a then little-known – and, after that, still little-known – computer, the IBM 9000, powered by a Motorola 68000 microprocessor:
Byte, January 1983 "IBM's 'Secret Computer: The 9000" by Chris Morgan: The best-kept secret of 1982 may have been that IBM makes a 68000 computer. If that surprises you, you're not alone. The unit, called IBM Instrument Computer System, is IBM's second major microcomputer product – the first, of course, is the IBM Personal Computer.The IBM 9000 is ideally suited to the laboratory. But it strikes me that the 9000's processor board could become the heart of a general-purpose microcomputer for the business market. As I said earlier, IBM is not commenting on this speculation.I think the 9000 is, in its quiet way, one of the most exciting new arrivals on today's microcomputer scene. I predict it will start showing up in all sorts of unexpected places. In one gesture IBM has legitimized a microprocessor that deserves more attention: the Motorola 68000.
Morgan was right about the Motorola 68000 chip. The IBM 9000? Not so much.
Byte also spent seven pages ruminating on where processors might go in the future, fantasizing about new instruction sets and then-unheard of transistor counts:
Byte, January 1983 "The Next Generation of Microprocessor: A proposed inexpensive microprocessor that can directly execute a high-level language" by Timothy Stryker: It will not be long before integrated-circuit manufacturers begin to come out with single-chip processors that can directly execute high-level-language instructions. When that happens, the resulting explosion in the availability of high-speed, high-quality software could make the current stage of the computer revolution look like a halfhearted warm-up exercise by comparison....it is amusing to note that Electronics magazine once ran as part of a "New Year's Wish List" the fervent hope that Intel Corporation's Gordon Moore be granted "inspiration on what to do with a chip holding 1 million transistors." That wish may be granted yet.
In the same issue, Byte delved into a subject that was relatively new at the time in a 10-page article by an author whose name makes one wonder about his security-conscious desire for anonymity:
Byte, January 1983 "Public Key Cryptography: An introduction to a powerful cryptographic system for use on microcomputers" by John Smith: New kinds of cryptographic systems are emerging that have incredible properties, which appear to eliminate completely some problems that have plagued cryptography users for centuries. One of these systems is public key cryptography.
And when was the last time that a computer magazine spent 17 pages comparing coding prime-number discovery routines using the Sieve of Eratosthenes algorithm?
Byte, January 1983 "Eratosthenes Revisited: Once More through the Sieve: A closer look at a benchmark prime-number program and various Pascal and C compilers" by Jim Gilbreath and Gary Gilbreath: We're not knocking Pascal; its place in the world as a versatile and safe language is quite secure. But C was more fun to work with.
I rest my case: both computing and computing magazines were quite different 30 years ago, which leads us to the following January, when things started to change in a big, big way – something Byte prophesied in a February 1983 review of Apple's Lisa.
Byte, January 1983 Review: ... the Lisa is the most important development in computers in the last five years, easily beating IBM's introduction of the Personal Computer in August, 1981.Apple knows that this machine is expensive and is also not unaware that most people would be incredibly interested in a similar but less expensive machine. We'll see what happens...
Well, with hindsight being 20/20 and after 30 years of history, we all know what did happen.