LuckyBackup

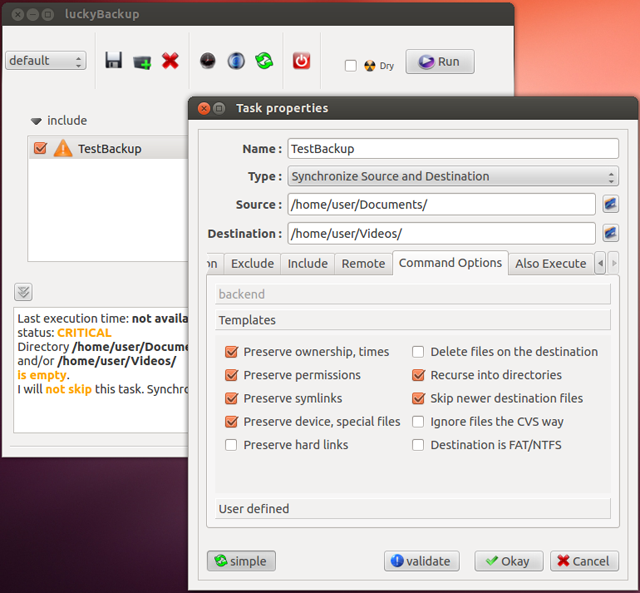
LuckyBackup isn't a backup utility in the traditional sense, but a front end for your old command-line friend rsync. As far as reliability goes, there is no substitute for rsync. That said, having a straightforward graphical interface on top is a very nice touch.
LuckyBackup is also far from complicated to use, all the options are clear so you can achieve anything from one-sided copy to incremental two-way synchronisation. Of course, the more advanced options of rsync are accessible too, but they'll stay out of the way until you need to find them. There's also a scheduler built-in and it will even email you when the job is done.
More info LuckyBackup on Sourceforge
PeaZip

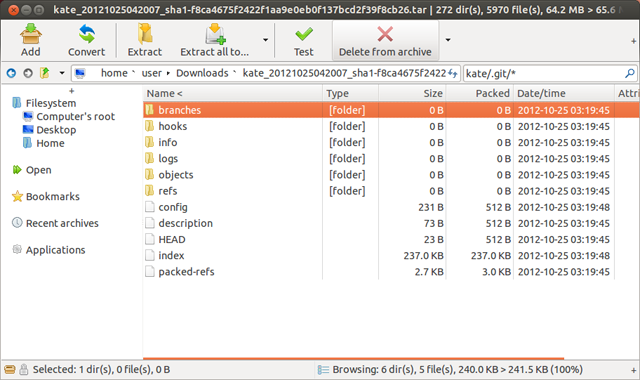
Although most Linux distributions come with an archive manager, such as File Roller in Ubuntu, PeaZip is much faster and works with more formats. With support for over 150 archive types when extracting and the ability to create 7Z, ARC, BZ2, GZ, PAQ, PEA, QUAD/BALZ, TAR, UPX, WIM, XZ, and ZIP files, the feature list is fairly comprehensive.
PeaZip even supports RAR extraction, an archiving option popular in the Windows world that's not so prevalent under Linux. In addition to managing other formats, PeaZip can also create secure PEA archives which ensure both privacy and authentication of the contents.
More info PeaZip on Sourceforge
