This article is more than 1 year old
What are quantum computers good for?
Forget cracking crypto, think modelling reality itself to help build a better one
The problem with trying to explain quantum computing to the public is that you end up either simplifying the story so far as to make it wrong, or running down so many metaphorical rabbit-burrows that you end up wrong.
So The Register is going to try and invert the usual approach, and try to describe quantum computing at a more materialistic level: how do you build one, and when it’s built, how do you use it? Hopefully, a concrete framework will make it easier to understand quantum computing along the way.
And we promise not to reiterate the story of Schroedinger ‘s cat. Not even once.
The basic design
Actually, a quantum computer is very easy to design. Its main systems are below.
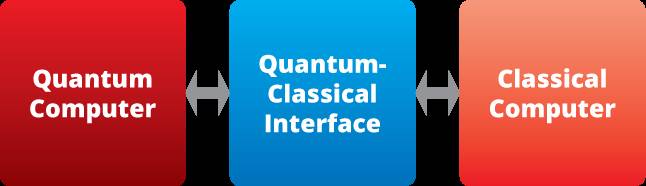
How to build a quantum computer. Image, Andy Davies, The Register
The classical computer is something we're all familiar with. The main point of having it there is because you – as the human trying to use the quantum computer – need something to interact with. We haven’t quite got so far as a nice GUI interface for what’s inside Schroedinger’s box.
The quantum computer is where the qubits live – those difficult creatures that, if we can control them properly, actually perform the quantum computation.
That leaves us the bit in the middle – the quantum-classical interface. It’s the cutoff between the quantum world and the classical world, which is why researchers call it the “Heisenberg cut”. It’s the place where classical information emerges out of quantum mechanics.
When it comes to describing quantum computing, that interface can be both easy and difficult to explain.
The mechanism for manipulating a qubit can be difficult to do (that’s what this year’s Nobel Prize in Physics was all about!) but it isn’t that hard to understand: it may be as “simple” as manipulating a mirror or a polarising filter. But just how “classicality” emerges from the quantum world occupies a lot of theoretical attention – the kind that needs long and deep study, and …
To be honest, it doesn’t matter all that much for this discussion. We know that classical emerges out of the quantum, because we’re here to argue about it. We can see that qubits behave like quantum phenomena: they exhibit entanglement and superposition, and those are the kinds of properties that give us quantum computers.
Next: The compiler
