This article is more than 1 year old
Liberator: the untold story of the first British laptop part 1
Taking over the typing pool
The Dragon team sets to work
The DTI, through its interest in seeking a future for the former GEC Dragon plant in South Wales, also helped bring Thorn EMI and Williams' group together, in the summer of 1984. That's how Williams remembers it - he and Peacock met a DTI representative in a motorway service station near the Severn Bridge, half way between London and South Wales, and the government man suggested they approach Thorn EMI. The DTI later gave Thorn EMI a "support for innovation" grant to support its bid for the CCTA contract.
A few days later, Williams and Peacock were invited to meet Colin Southgate, then Group MD of Thorn EMI's IT division. "So we went down, met him, told the whole story and went through some budget projections and he said, 'yes'. He was one of those guys who make decisions very quickly, and he said in that meeting, 'I'm going to hire you'."
"The attraction to Thorn was they they were inheriting not a group of individuals but a team that had all the required disciplines to take on a project like the Liberator," recalls Jan Wojna.
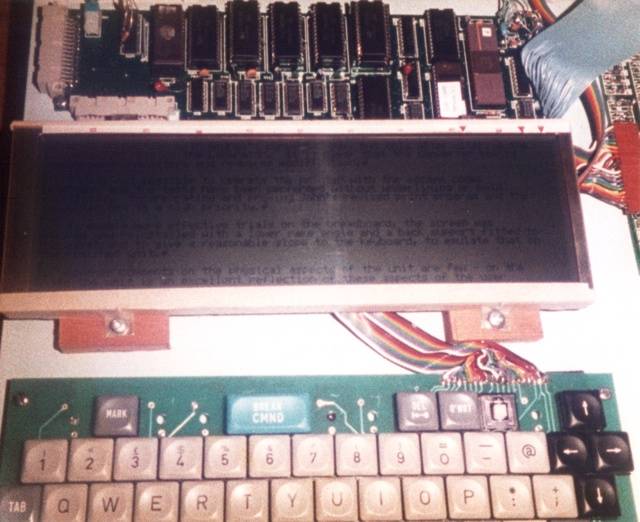
It lives!
Source: Bernard Terry
"We were an unusual team," adds Derek Williams. "You wouldn't normally have someone like John Peacock, who's a chartered accountant, involved in the development group like this. But John has many other skills apart from financial. He's a really good wheeler dealer is John, and so he basically managed the purchasing side of things. John was very innovative in getting the cost of components down."
There was, Wojna remembers, a small period between Dragon's collapse and work on the new machine commencing at Thorn EMI - including the time taken to establish a development lab - but then "once all the basics had been sorted out - accommodation and things like that - it was a case of working out how we were going to turn this into a reality: [asking] what we need from the hardware, what we need from the software, what are the constraints, what are the requirements and what's the current technology available that would help us achieve that."
Thorn EMI itself the advantage of a presence in South Wales. And its plant in Treorchy, Glamorgan was under threat: by the early 1980s it was punching out dials for rotary phones - the operation was called Thorn EMI Dynatel - but was being undercut by Taiwanese rivals, as was so much of British manufacturing at that time. The factory might close, but if the proposed mobile text processor could be produced there, workers' jobs would be saved.
Financially, the CCTA text editor project was easy for Thorn EMI to accept, says John Peacock, because it was low risk. It could afford to chance "half a million quid and, in the end, more like £350,000 after the government grant" on the project going awry.
Whether it was DTI civil servants concerned by rising unemployment in the area; Thorn EMI's ability to persuade the CCTA that, with Derek Williams' team on board, it was best placed to deliver the mobile computer on time and on budget; Williams and Peacock's entrepreneurial chutzpah; or a mixture of all these factors, in August 1984, the CCTA gave Thorn EMI the go-ahead to design the Liberator and manufacture it at Treorchy.
Had GEC Dragon survived, the engineers might have considered basing the new machine on the technology they were preparing for future Dragon computers: the Motorola 6809E processor and its fully 16-bit successors, and Microware's Unix-like OS-9 operating system. At Thorn EMI, however, the team started afresh. Bernard Terry had already provided a broad statement of the problem they needed to solve - devise a text processing system civil servants could use to create documents away from their desks and later print out those documents - and it was up to them to spec up and create the machine.
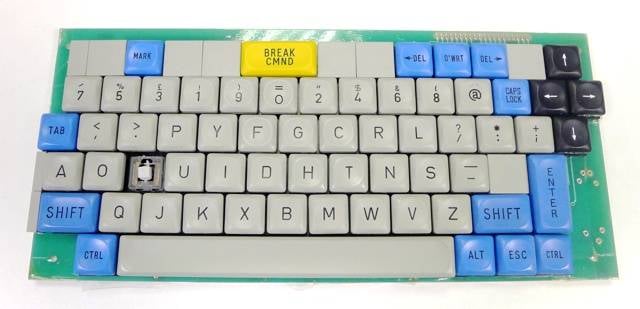
The prototype's keyboard
The were given very little time to do so. Peacock, Linney, Wojna and Smeed all separately recall Derek Williams promising Thorn EMI chiefs that he and his team would have the prototype up and running within six months - a timetable pointing to completion by January 1985, at which point the CCTA was expecting to take possession of an initial 40 units. The pledge was treated with some skepticism by the powers that be, but it was one that the team, fuelled by coffee, adrenalin and a youthful drive to succeed, were able to make good.
At the time, the best choice for a low-power processor - clearly an essential requirement for a battery powered machine intended to free users from being permanently tethered to a power supply - was Zilog's ageing Z80A. John Linney recalls that other, more advanced microprocessors were briefly considered, including the Intel 8088 used in the IBM PC, but quickly rejected because of their relatively high power consumption.
"The Z80A could be put into a very low-power mode and [you could] wake it up with an interrupt," recalls Jan Wojna. "Whenever possible, we put the whole thing into this low-power mode or make it run more slowly."
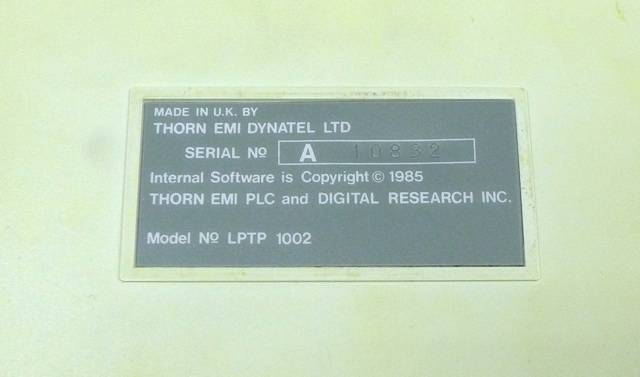
The label says Digital Research, and the OS was CP/M, but using the Liberator, you'd have never known it
As the original Liberator Technical/Service Manual notes: "Great care has been taken both in software and hardware to keep the operating, standby and backup power consumption to a minimum, eg. in the operating mode the Z80 spends inactive periods in a 'halt' state (min. power consumption state, supply current about 65mA), when in standby mode power is disconnected from the Z80 system and the I/O processor [is put] in a 'sleep' condition (supply current <1mA)."
With the processor selected, the operating system effectively chose itself, says Linney. The team could have built one afresh, but it was easier and, crucially, less time-consuming to license one. For the Z80A, the only real choice was Digital Research's CP/M. ®
Part Two: The Liberator is launched
Part Three: Into the maelstrom

