This article is more than 1 year old
A history of personal computing in 20 objects part 2
The 1980s to the Present
Power computing...
GRiD 1100 Compass
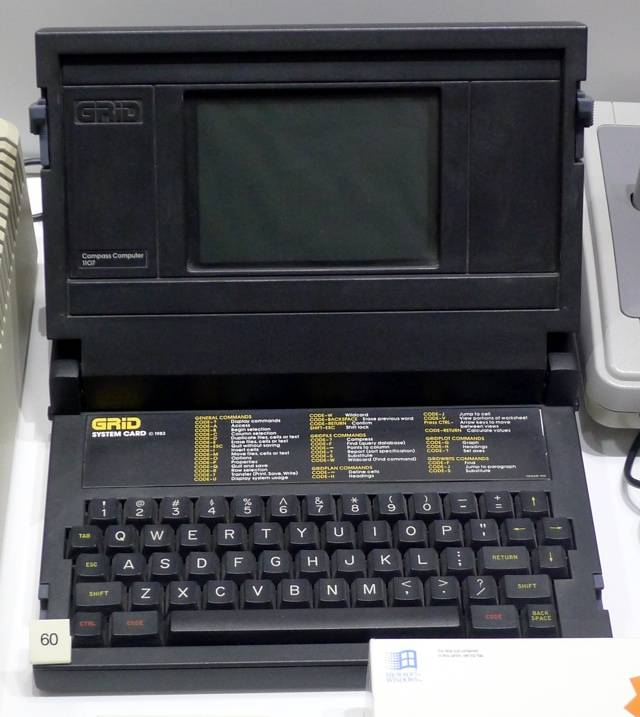

Monstrously expensive and aimed at advanced military and aerospace applications - Nasa was an early customer - GRiD’s Compass, released in April 1982, was the world’s first clamshell computer and thus the template for the notebook computer. Designed by Briton Bill Moggridge (1943-2012), the Compass was based on an Intel 8086 processor running GriD’s own GRiD-OS operating system. It had a 320 x 340 electroluminescent display and 3409KB of non-volatile magnetic ‘bubble’ memory. There was a 1.2Kb/s modem on board too.
Apple Macintosh
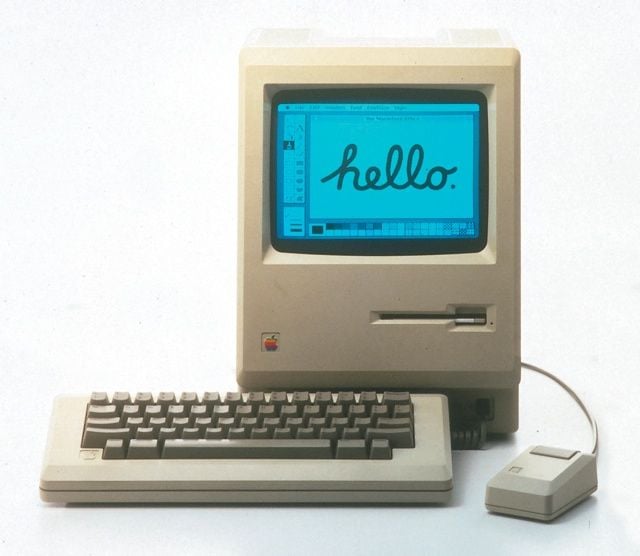

The Mac didn’t introduce the graphical user interface - the Xerox Alto did - and it wasn’t even Apple’s first computer with a GUI - that was the Lisa - but it was the personal computer that did the most to popularise the graphical user interface and is one of very few personal computer device brands still going strong today, 28 years after its 1984 launch. Microsoft’s Windows would come to eclipse the Mac OS in volume, and despite rival GUIs like Gem, for a brief period through the late 1980s and early 1990s, the Mac defined how a modern GUI should work and look. It also provided the foundation for the desktop publishing revolution, which changed forever the economics of book and periodical publication, and arguably showed that any content could be produced on a computer.
Acorn Archimedes


Acorn’s successful BBC Micro, derived from its unreleased Proton machine, kept the company going through the mid-1980s and helped it survive the very tough years of 1984 and 1985. But the Micro wouldn’t last forever, and its 6502 processor was by then long in the tooth. Rather than buy in an alternative, Acorn chose to create its own. The result was the ARM chip, and it was first implemented in the Archimedes in 1987. The chip’s designers, Sophie Wilson and Steve Furber, were attracted to the then vogue for Reduced Instruction Set Computing (Risc), and so the Archimedes became the first mass-market Risc-based personal computer.
