This article is more than 1 year old
A history of personal computing in 20 objects part 1
From the 17th Century to the 1970s
Onto the Desktop...
Xerox Alto
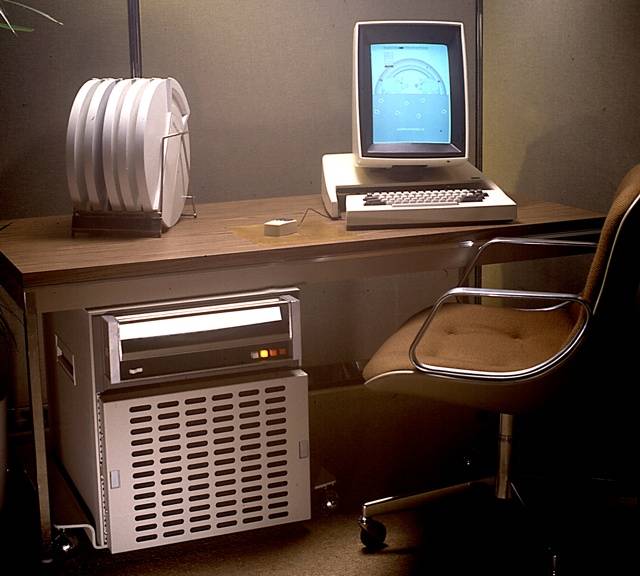

The Alto was an experimental machine built by boffins in Xerox’s Palo Alto Research Centre (PARC) in the early 1970s to explore new thinking in user interface design, and while never made available commercially - Xerox would sell the Star, a version of the Alto, in 1981 - a couple of thousand were made for use by Xerox staff and some were donated to universities and research facilities. Arguably the first personal computer - though some historians consider it a minicomputer - it was also the first to feature a graphical interface controlled by a mouse and to incorporate networking.
MITS Altair 8800


The Altair 8800 may not have been the world’s first personal computer aimed at hobbyists rather the scientists and engineers - that was 1973’s Scelbi-8H - but it was the first of the switches’n’lights home micros to gain wide appeal. Manufacturer MITS (Micro Instrumentation and Telemetry Systems) had been founded in 1969 to build electronics for tracking model rockets, though it soon turned its attention to programmable-calculator kits. A single-user computer was the logical next step, and work began in 1974 on an Intel 8080-based machine to be sold in kit form. A crucial tie-in with US magazine Popular Electronics helped put the Altair in front of thousands of potential users in December 1974. The assembled unit was a pain to program: instructions were fed in by flipping switches on the front. That changed when a small, two-man company called Microsoft was hired to write a Basic interpreter for the machine, fed in on paper tape.
Apple II
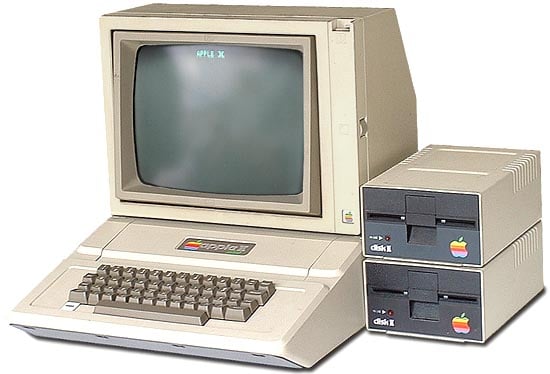

Launched in April 1977 and shipped two months later, the Apple II is probably the member of a small group of first personal computers launched that year - others include the Commodore Pet and Tandy’s TRS-80 - that did the most to take the technology beyond the reach of hobbyists and into the mainstream. The work of Steve Wozniak (1950-) and Steve Jobs (1955-2011), the Apple II was equipped with a 6502 CPU and 4KB of Ram, colour graphics and - an interesting innovation - expansion slots, the Apple II proved hugely popular, despite being priced well above the competition, largely because it quickly established an extensive library of third-party software users could run to get things done.
In Part Two, Tomorrow: Objects 11-20 - the 1980s and beyond
