This article is more than 1 year old
A history of personal computing in 20 objects part 1
From the 17th Century to the 1970s
Archaeologic Personal computing. Personal. Computing. We take both aspects so completely for granted these days, it's almost impossible to think of a time when computing wasn't personal - or when there was no electronic or mechanical computing.
To get from there to here, we've gone from a time when 'computers' were people able to do perform complex calculations themselves, through mechanical systems intended to do the work for them and then to powered machines able to automate the process. These led to systems that could be programmed to perform not only mathematical tasks but to store and retrieve other forms of data, taking us right up to desktop devices for a one-on-one interaction with computing power.
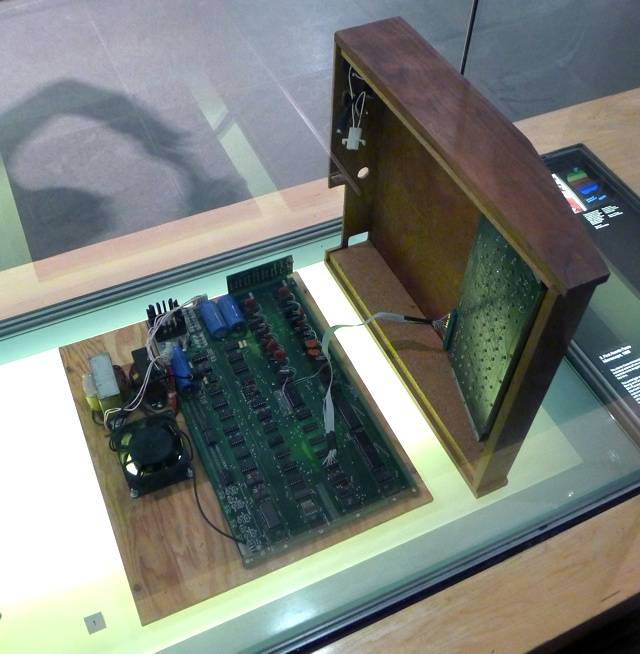
I, Apple I
Since then, that power has been compressed into smaller, more convenient packages: laptops, tablets and smartphones.
What a trip. In memory of the many people who have help us along, here then are some of the key stages of that journey, represented by the 20 objects that, to us, most embody the steps that brought us to where we are today.
It's not a comprehensive list - and feel free to comment with the devices you think we should have included - but here are the first ten of our 20 items, from the early days up to the end of the 1970s. Part two will bring us from the 1980s to the present day.
Computing's Prehistory...
Napier’s Bones


As if introducing logarithms and evangelising the use of the decimal point weren’t enough, 16th Century Scottish mathematician John Napier (1550-1617) also devised a calculating machine able to multiply and divide. It could even work out square roots. There was initially no mechanism as such: just a series of rods - the ‘bones’ - marked with two columns of numbers. To calculate a multiplication, line the rods up side by side so the figures at the top of each show the digits in the multiplicand. A column of numbers on the left side of the apparatus provides the multipliers: read across the appropriate row, right to left, adding numbers grouped by diagonal lines, to generate the digits of the answer. Division is performed in a similar way. The rods were soon replaced by cylinders, each of which replicated all nine rods and could be rotated to ‘set’ the a given digit in the multiplicand.
Babbage’s Difference Engine


Charles Babbage (1791-1871) first came up with the notion of a calculating machine capable of printing out perfect logarithm tables in 1812 at the tender age of 21. Seven years later, he set about producing such a device and, in 1822, he and his tame mechanic had put together the first Difference Engine, a clock-like assembly of interlocking cogs able to calculate squares and solve quadratic equations. It worked sufficiently well for the government and other institutions to invest in the production of a large, more capable version. It proved too complex and was never completed - the project was effectively abandoned in 1834. By this point, despite many personal and professional setbacks, Babbage had his eye on the Difference Engine’s successor: a multi-function, programmable ‘Analytical Engine’. It too was never built, but nonetheless prompted the writing of first computer program.
