This article is more than 1 year old
How to get your bust in good shape
Got a 3D printer – now what?
Seeing red
A retractable tape measure set to 40cm is quite useful to have around. For scanning a person you’ll need to walk all the way around them, so make sure the path is clear. Putting the Kinect on a table and spinning the person works but you then to miss the top of the head and under the chin. Unfortunately the room my computer is in has a very low ceiling and the tops of heads often pose a problem.

The image windows the view from both the normal and infra red cameras
The instal package includes some scripts to run the software from a command line. A separate video window shows both the image from the video camera and the model grabbed from the infrared. All the processing is done in real time. If your video card is fast enough you can stitch in real time.
Scanning slowly enough and capturing all the angles without the scanning losing track is a patience sapping activity. The software will often pick up the tracking but if it fails you have to start again. The model has to keep still while you are doing it and my son proved incapable of sitting still, holding his guitar without strumming, so a friend sat in.
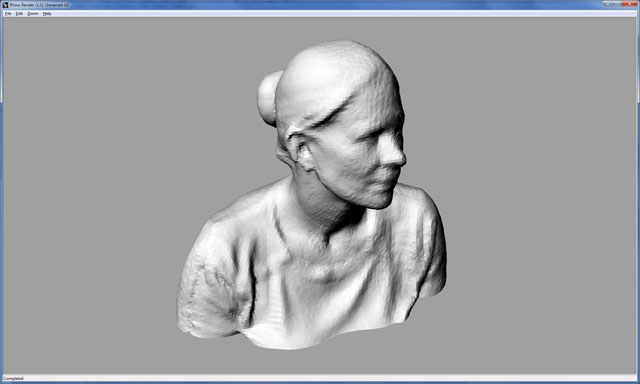
A rendered image of the scan
Moving the sensor back a tad and waiting seemed to improve the odds of re-acquiring the tracking. It doesn’t seem to be particularly sensitive to lighting, but we kept finding odd patches which didn’t scan. This turned out to be warm spots generated by the halogen lights in the room, which gave the infra-red problems.
Pulling the mesh into a modelling program – Rhino 4.0 in this case – shows that it’s much less noisy than the images coming out of 123D Catch, but the resolution isn’t as good.
What these two approaches to 3D scanning show is that there is real progress being made in the emerging world of hobbyist 3D scanning. It’s still very much at the stage of being used by people who understand the technology rather than artists who just want a means to an end, when we see booths in shopping centres who offer to turn your family into chess pieces we’ll know the technology has matured. ®
Simon Rockman, aside from writing about curious tech, is a purveyor of phones for older users. You can read his Fuss Free Phones blog here.
