This article is more than 1 year old
Hands on with BB10: Strokey dokey
No time for 'Back' buttons - we're headed into the FUTURE
Apparently crafted specifically for Roger Federer
Typing "Hello my" called up suggestions for "name". Even better, typing "Hello my name is Roger" got the phone suggesting "Federer" as the next word. It will be able to provide this in three different languages simultaneously, for multi-linguists.
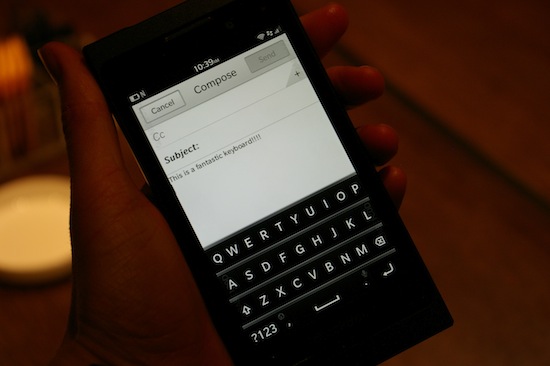
BB10's keyboard: Note that the BlackBerry rep chose this enthusiastic message, rather than your humble Reg hack
Another stand-out feature on BB10 is the time-shift camera. It's a Minority Report-style feature that allows you to rewind parts of your photo to create a finished image that features bits from different times.
The camera takes several photos before you click the shutter and is able to "rewind" through them, so you can get all the bits to the perfect place. If someone had their eyes closed when you pushed the shutter, you can circle off their face and "rewind" that section of the photo to when they were making the right expression.
A final interesting feature - one for the business clients - is an option to partition the phone into sealed work and personal areas.

BB10's Peek mode allows you see your message centre with a swipe.
The password-protected "work" area can include files and apps that are not accessible on the "personal" side of the divide, and can be controlled by the IT department. That side can be bricked remotely by the company, if for example someone leaves, without affecting the personal side of the phone.
IT can configure whether personal notifications arrive in the work mode or not.
RIM reps kept schtum on several key aspects of the OS, declining to answer questions about what partners are on board for search, maps or the music store: "We can't tell you that".
What they could tell us is that BB10 is for "successful" people. Enright explained:
It's for people who want to get on and be successful. That could be a businessman or it could be a 12 or 14 year old who wants to be successful in school and successful in their social group.
®
